What is biometric access control in data security?
Biometric access control uses unique physical characteristics—in our case, palm vein patterns—to verify identity before granting access to data centers and server rooms. Unlike cards or PINs that can be shared, stolen, or forgotten, biometric credentials are tied to the individual and cannot be duplicated. Our system scans the vein pattern beneath the skin using near-infrared light, creating a template from 5 million data points. This contactless method takes under 2 seconds and achieves 99.99991% accuracy with built-in liveness detection to prevent spoofing.
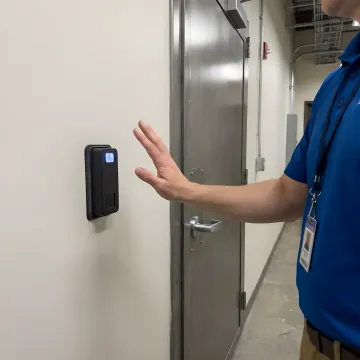
How does biometric access control integrate with existing data center security systems?
Our ePortPass system integrates seamlessly with your current infrastructure through industry-standard Wiegand or OSDP protocols. It works with existing access control panels, electric strikes, mag-locks, turnstiles, and gate controllers without requiring a complete system replacement. The biometric readers can be installed on doors, server rack cages, equipment cages, and entry points. You maintain your existing access control software and simply add biometric verification as an additional authentication factor. Setup is straightforward and causes minimal operational disruption.
Can biometric systems prevent tailgating and credential sharing in data centers?
Yes, biometric verification eliminates tailgating and credential sharing because each person must authenticate individually using their unique palm vein pattern. Traditional card systems allow one person to badge in and hold the door for others. With our system, every individual must present their palm for scanning, creating an indisputable record of who entered and when. The system can be configured to require one scan per person through turnstiles or mantraps. Real-time alerts notify security staff of any denied access attempts or unusual patterns, such as multiple people trying to use the same credentials.
What happens if a data center employee leaves the company or loses access privileges?
When an employee is terminated or access privileges are revoked, their biometric template is immediately deactivated in the system. Unlike physical cards that might not be returned, or passwords that might be shared, the former employee cannot gain access even if they return to the facility. Our system provides real-time alerts if terminated employees attempt entry, creating a complete audit trail of the denied attempt including timestamp and location. For temporary contractors or vendors, you can create time-bound, location-specific permissions that automatically expire without manual intervention.
How quickly can biometric access control be deployed in an operational data center?
Installation is designed for minimal disruption to your operations. Most data centers complete deployment in days, not weeks. The hardware mounts easily to existing doors, turnstiles, and gates. Because our system integrates with your current access control infrastructure via standard protocols, there's no need to replace existing panels or reconfigure your entire security network. We can phase deployment by zone—starting with your most sensitive areas like primary server halls or network operation centers—allowing you to maintain operations throughout the installation process.
What audit and compliance capabilities does the biometric system provide?
Our system creates comprehensive, tamper-proof audit trails for every access event. Each entry and exit is logged with biometric verification confirmation, timestamp, location, and duration of access. Reports can track access patterns, identify unusual activity, and demonstrate compliance with standards like SOC 2, HIPAA, PCI-DSS, or NIST frameworks. The system logs denied access attempts, including who tried to gain entry and when. All data is encrypted and can integrate with your SIEM or security monitoring platforms for centralized visibility across multiple facilities.
Is contactless palm vein scanning hygienic for high-traffic data center environments?
Absolutely. Our contactless palm vein technology requires no physical contact with the scanner surface, making it ideal for shared environments. Users simply hold their hand 2-4 inches above the reader for verification in under 2 seconds. This eliminates hygiene concerns associated with fingerprint scanners or shared keypads. The contactless nature also reduces wear and tear on equipment, extending hardware lifespan. Since the technology scans beneath the skin using near-infrared light, external conditions like dirt, moisture, or minor cuts don't affect accuracy.
Can the biometric system provide multi-factor authentication for enhanced security?
Yes, our ePortPass system supports one, two, or three-factor authentication configurations based on your security requirements. You can combine palm vein biometrics with proximity cards and PIN codes for maximum protection in your most sensitive areas. For example, entry to primary server halls might require card plus biometric, while access to critical infrastructure zones like power distribution or network cores could mandate all three factors. The system is flexible, allowing you to assign different authentication levels by zone, time of day, or individual clearance level.