What are the 5 D's of access control?
The 5 D's of access control are Deter, Detect, Deny, Delay, and Defend. Our biometric solutions address all five: deterring unauthorized access attempts through visible security presence, detecting entry attempts in real-time with instant alerts, denying access to anyone without proper biometric credentials, delaying potential intruders through multi-factor authentication requirements, and defending critical assets with audit trails and accountability measures that create comprehensive security documentation for incident response and investigation.
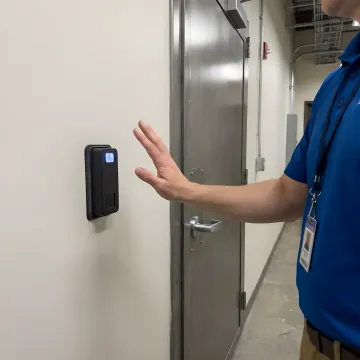
How to physically secure a server room?
Physically securing a server room requires layered access control combining biometric identity verification, controlled entry points with electric strikes or mag-locks, real-time monitoring with entry/exit audit trails, and visitor management protocols. Our contactless palm vein systems provide the strongest layer by verifying identity with 99.99991% accuracy, preventing credential sharing and tailgating, creating time-stamped access logs, and integrating with existing security infrastructure. Add multi-factor authentication (biometric + card + PIN) for maximum protection of mission-critical server environments.
How does contactless palm vein biometric technology work?
Palm vein biometric technology uses near-infrared light to capture the unique pattern of veins inside your palm. Because the pattern is internal and requires blood flow, it checks for liveness during every scan and cannot be spoofed with photos or fake fingerprints. The system creates an identity from 5 million unique points—a pattern shared by no one else, not even identical twins. Users simply hold their hand over the reader for under 2 seconds. The contactless nature eliminates hygiene concerns while providing the most accurate biometric verification available at 99.99991% accuracy.
Can your system integrate with our existing access control infrastructure?
Yes, our ePortPass system is designed for seamless integration with existing access control systems through industry-standard Wiegand or OSDP protocols. It can interface with your current card readers, electric strikes, mag-locks, turnstiles, and gate controllers without requiring complete infrastructure replacement. The system can work standalone, replace insecure RFID cards entirely, or integrate cards into a multi-factor authentication approach. We can also connect multiple locations on a secure subnet or VPN using static IPs for centralized management across your organization.
What kind of audit trails and reporting does the system provide?
Our system creates comprehensive entry audit trails documenting every access event with timestamps for entry, exit, and duration. You receive real-time alerts for denied entry attempts, unusual access patterns, or former employees attempting access after termination. The reporting system tracks who accessed which locations and when, provides trend analysis for management review, and creates an indisputable record for compliance and security investigations. All data can be accessed centrally across multiple locations for a complete operational picture of your security posture.
How do you handle temporary access for vendors and contractors?
Our system allows you to enroll vendors and contractors with time-bound, location-specific permissions that automatically expire. You can set access windows (specific days and times), restrict access to designated zones only, and receive notifications when temporary credentials are used. The biometric verification ensures the enrolled individual is actually the one accessing the facility—preventing shared credentials or badge borrowing. When the contract period ends, access automatically terminates without requiring physical credential retrieval, and you maintain complete audit trails of all vendor activity.
What happens if someone tries to access the server room without authorization?
Unauthorized access attempts trigger immediate real-time alerts sent to designated security personnel. The system denies entry automatically, logs the attempt with timestamp and location data, and can capture additional context like which credential was attempted. You can configure escalating responses for repeated denial attempts from the same individual or location. All denied access events are documented in the audit trail for security review and investigation. The system's 99.99991% accuracy ensures legitimate users aren't falsely denied while unauthorized individuals have virtually no chance of gaining access.
What is the implementation timeline and training requirement?
Implementation is straightforward because our units attach easily to existing doors, turnstiles, gates, and access points without extensive construction. Most installations are completed within days depending on the number of entry points. The system is designed to be user-friendly—enrollment takes seconds per person, and users need minimal instruction (simply hold hand over reader). Administrative training for security personnel typically requires just a few hours to cover enrollment procedures, alert management, and reporting functions. We provide comprehensive support during implementation and ongoing technical assistance.