Introduction
Hospitals operate 24/7 with thousands of staff, patients, vendors, and visitors moving through dozens of sensitive zones daily — making them both among the most open and most security-critical environments in existence. A single facility houses emergency departments with public access, neonatal intensive care units with strict entry protocols, pharmacies storing controlled substances, and server rooms protecting millions of patient records. Managing who can enter which space — and when — is a daily operational necessity with measurable consequences.
The real value of hospital access control systems shows up in concrete outcomes: fewer security breaches, faster emergency response, reduced medication theft, and maintained regulatory compliance. Healthcare facilities account for 72.8% of all workplace violence incidents in private industry, and data breaches in this sector cost an average of $9.77 million per incident — the highest of any industry for 14 consecutive years. Access control directly addresses the vulnerabilities driving these costs.
This article examines the measurable advantages effective access control delivers, the consequences of weak controls, and the best practices that separate implementations that protect from those that fall short.
TL;DR
- Hospital access control manages who enters physical areas or accesses digital systems, enforcing role-based permissions across complex, 24/7 facilities
- Core advantages include protecting patients and staff in high-risk zones, maintaining HIPAA-compliant audit trails, and eliminating forged or shared credentials
- Weak controls lead to medication theft, data breaches, regulatory fines up to $2.13 million per violation category, and compromised patient safety
- Best practices include role-based access, layered credentials for high-risk zones, regular permission audits, and integration with visitor management systems
- Contactless palm vein biometrics verify identity in under 2 seconds — no cards, PINs, or passwords that can be lost or stolen
What Is Hospital Access Control?
Hospital access control is the combination of systems, policies, and technologies that determine who can enter which physical spaces — or access which digital resources — within a healthcare facility, and when. The definition is straightforward, but implementation spans two distinct layers that modern hospitals must manage simultaneously.
Both layers work together to form a complete security posture:
- Physical access control: doors, wards, pharmacies, medication storage areas, operating rooms, and restricted clinical zones
- Logical (digital) access control: electronic health records, scheduling systems, imaging software, and other systems housing protected health information
Modern platforms increasingly unify both layers under a single management interface, keeping security policies consistent across the facility.
Access control exists to deliver outcomes, not to satisfy a technology checklist. Patients are protected from unauthorized entry into sensitive care areas. Staff work without unnecessary friction — a nurse's permissions cover the medication room but not the server room, and those access rights update automatically when her role changes. Facilities can also demonstrate accountability to regulators at any time through complete, timestamped records of who accessed what and when.
Key Advantages of Hospital Access Control Systems
The advantages below are grounded in operational impact — cost reduction, risk mitigation, compliance assurance, and patient safety — rather than theoretical security benefits. Each directly influences metrics that healthcare administrators and security directors track and report.
Protecting Patients and Staff Through Controlled Access Zones
Role-based and zone-based access rules ensure that only authorized individuals can enter high-risk areas — NICUs, psychiatric wards, operating rooms, ICUs, and medication storage — at any hour of the day.
How it works in practice:
- Each staff member receives credentials tied to their specific role
- Access permissions update automatically when roles change through integration with HR systems
- In emergencies, entire zones can be locked down or selectively unlocked from a central dashboard in seconds
- Denied access attempts trigger real-time alerts to security teams
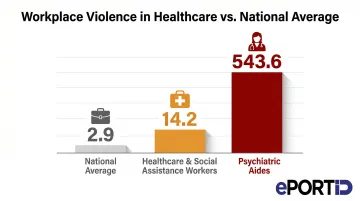
Unauthorized access to sensitive zones is directly linked to patient abductions, medication theft, and staff assault incidents. Healthcare and social assistance workers experience workplace violence at a rate of 14.2 incidents per 10,000 full-time workers — nearly five times the national average of 2.9. Psychiatric aides face an even more severe burden, with 543.6 incidents per 10,000 workers.
Hospitals that restrict zone access based on role dramatically reduce the probability of both accidental harm and intentional misconduct. Controlled access also protects staff by limiting who can enter high-stress clinical areas, reducing confrontations and creating a more accountable environment where individuals know their movements are monitored and logged.
Infant abduction data from the National Center for Missing & Exploited Children shows that of 344 infant abductions tracked from 1964 through 2024, 141 occurred in healthcare facilities. Hospital abductions peaked in the late 1980s and early 1990s but have declined to near-zero in recent years following improved security measures, including access control systems that restrict entry to maternity wards and nurseries.
KPIs impacted: Unauthorized entry incidents, medication loss or diversion rate, staff assault reports, security response time to breaches.
When this advantage matters most: In large, high-traffic hospitals where public access to lobbies and waiting areas makes internal zone security critical; in facilities with psychiatric wards, pediatric units, or pharmacies that require strict entry controls at all hours.
Ensuring HIPAA Compliance and Generating Audit-Ready Records
HIPAA's Security Rule and Privacy Rule both require healthcare facilities to physically restrict access to systems and spaces where Protected Health Information (PHI) is stored or accessible. Access control systems fulfill that requirement while simultaneously generating the audit evidence to prove it.
How it works in practice:
Every access attempt — whether successful or denied — is automatically logged with a timestamp, credential ID, and location. This creates an indisputable, continuously updated record that can be retrieved for audits, breach investigations, or regulatory reviews without manual effort.
When a potential breach occurs, security teams can identify who accessed what, when, and from where — turning a weeks-long investigation into a rapid query.
HIPAA violations carry significant financial penalties. Civil monetary penalties range from $141 per violation for lack of knowledge to $2,134,831 per violation for willful neglect not corrected, with annual caps reaching $2.13 million per violation category. HHS Office for Civil Rights has resolved 370,578 HIPAA cases and collected $144.88 million in settlements and penalties, with "lack of safeguards" ranking as the #2 most frequent compliance issue.
The audit trail infrastructure extends beyond HIPAA. Hospitals face overlapping compliance obligations, and the same logging and reporting capabilities serve all of them:
- Joint Commission reviews — access records demonstrate physical security controls
- State regulations — timestamped logs satisfy jurisdiction-specific PHI protection requirements
- ISO 27001 frameworks — access governance data maps directly to audit evidence requirements
- NIST SP 800-66 Revision 2 — specifically maps HIPAA's physical access requirements to recommended controls including account management, access enforcement, and audit logging
KPIs impacted: Compliance audit pass rate, time to close breach investigations, regulatory fine incidence, number of unresolved access anomalies.
When this advantage matters most: For any facility handling PHI (which is all hospitals); especially impactful during system expansions, staff turnover events, or active regulatory reviews where access governance must be demonstrable on demand.
Eliminating Credential Fraud and Preventing Unauthorized Access
Shared key cards, lost fobs, and buddy-punching — where one employee badges in on behalf of another — represent significant vulnerabilities in hospital access environments. In high-stress, shift-based workplaces, these shortcuts become habits that erode security over time.
How it works in practice:
Contactless biometric solutions such as palm vein scanning verify identity from vein pattern data points beneath the skin surface — anatomy that cannot be transferred, duplicated, or forgotten. ePortID's contactless palm vein technology derives identity from 5 million unique vein pattern points with 99.99991% accuracy, completing verification in under 2 seconds without physical contact. The credential lives in the person, not in a card or fob that can walk out the door.

The American Payroll Association estimates that over **75% of companies lose money from buddy punching**, with time theft costing businesses 1.5% to 5% of gross payroll annually. In healthcare facilities with large staff rosters and rotating shifts, this translates to substantial payroll losses.
A peer-reviewed national survey of hospital pharmacies found that only 23.7% of health systems restrict controlled substance area access by work schedule, and over 40% update access codes only "for cause" rather than on scheduled cycles. This weak physical access governance directly enables medication diversion, which has resulted in settlements ranging from $2.3 million (Mass General) to $7.75 million (McLaren Health).
Biometric verification creates accountability by binding every access event to a confirmed identity rather than a transferable credential. This narrows the window for insider threats and establishes a culture of individual responsibility where access cannot be delegated or shared.
The contactless nature of palm vein scanning also supports infection control goals — eliminating shared-touch keypads and card readers that research shows can harbor pathogens including MRSA and C. difficile in clinical environments.
KPIs impacted: Verified-identity access rate, buddy punching incidents eliminated, medication theft or supply loss rate, payroll accuracy, credential-related security violations.
When this advantage matters most: In facilities with large staff rosters, rotating shifts, and high turnover; in high-value access zones such as pharmacies, server rooms, surgical suites, and data centers where the cost of a single unauthorized entry is severe.
What Happens When Hospital Access Control Is Ignored
Facilities that rely on outdated or absent access control systems face a predictable set of consequences — most of which surface weeks or months after the damage is done.
Common consequences:
Unauthorized individuals gain entry to patient wards, medication rooms, or data centers — often only discovered when inventory doesn't match records, a former employee turns up in a restricted area, or a breach investigation uncovers months of unreported access.
Without automated logging, HIPAA audits and breach investigations stall immediately. Healthcare breaches take an average of 213 days to discover — 19 days longer than the cross-industry average — because missing audit trails extend exposure windows by weeks.
Lost keycards, expired visitor badges, and access credentials that were never revoked after an employee departure create entry points security teams can't easily identify. The peer-reviewed diversion study found that over 40% of hospitals only update access codes "for cause" rather than on scheduled cycles, leaving active entry points open indefinitely.
Without automated alerts and zone-based restrictions, security teams respond to incidents instead of preventing them — response times climb, costs rise, and the likelihood of a severe event compounds over time.
Manual access management breaks down as hospitals expand — inconsistent enforcement across multiple facilities or acquisitions creates compliance gaps that are difficult to audit and costly to correct.

Best Practices for Hospital Access Control
Access control works only when it reflects how the facility actually operates — kept current, enforced consistently, and reviewed as staff and workflows change. These five practices form the operational foundation.
RBAC: Tie permissions to job function, not individual requests A pharmacist accesses the medication room; a receptionist does not. When RBAC is integrated with HR systems, permissions adjust automatically as roles change — no manual cleanup required. NIST SP 800-66 Revision 2 recommends this approach under the Principle of Least Privilege.
Match credential strength to zone sensitivity Low-sensitivity areas (lobbies, general corridors) can use a key card or PIN. High-risk zones — pharmacies, ICUs, server rooms, medication storage — require multi-factor or biometric verification. ePortID's palm vein systems support two- and three-factor authentication (palm vein + RFID card + PIN), letting hospitals apply the right level of control to each zone without over-securing lower-risk areas.
Time-limit and zone-restrict every temporary credential Vendor and visitor credentials should expire automatically and restrict movement to relevant areas only. Log all temporary access and sync with scheduling systems to catch overstays before they become incidents. Joint Commission standards require identification systems for patients, staff, and visitors — structured visitor management satisfies this requirement directly.
Connect access events to surveillance and emergency response Access logs become far more useful when they trigger action. Linking door events to surveillance cameras, environmental sensors, and lockdown protocols converts access control from a passive record into an active response system. ePortID's contactless biometric platform integrates into existing critical infrastructure frameworks — a capability refined through deployments with the US Navy, Army JTF, Marine Corps, and Port Authorities over two decades.
Audit permissions quarterly — don't wait for an incident At minimum quarterly, review all active credentials and remove anything inactive, expired, or over-permissioned. Accumulated "ghost" access — former employees, rotated vendors, role-changed staff — is one of the most common vectors for unauthorized entry in healthcare facilities. Research confirms it: hospitals that schedule routine access code updates, rather than updating only after incidents, maintain significantly stronger medication security.

Conclusion
Hospital access control delivers value on three fronts that build on each other over time:
- Patient and staff safety — restricting sensitive zones to verified personnel only
- Regulatory compliance — creating the audit trails and accountability records HIPAA and Joint Commission standards require
- Credential integrity — replacing cards and PINs with identity verification that can't be shared, lost, or spoofed
These advantages compound over time. A well-implemented system grows more valuable as the facility expands, staff turns over, and regulatory scrutiny tightens. A neglected one moves in the opposite direction: the attack surface widens, compliance exposure grows, and security teams spend more time managing workarounds than actual threats.
That's why access control works best as an ongoing operational practice, not a fixed installation. Regular audits, role reviews, and technology updates keep the system aligned with how the facility actually operates. Hospitals that approach it this way — treating access control as infrastructure to maintain rather than a project to complete — are the ones that stay ahead of both security threats and compliance requirements.
Frequently Asked Questions
What are the 5 D's of access control?
The 5 D's — Deter, Detect, Deny, Delay, and Defend — describe a layered security approach. In hospitals, this translates to visible deterrents, real-time access alerts, credential-based locks, multi-checkpoint authentication, and coordinated response protocols when breaches occur.
What are access controls in healthcare?
Healthcare access controls are the policies, systems, and technologies that govern who can enter physical spaces or access digital systems like EHRs. They span both physical security (doors, restricted zones) and logical security (logins, database access) to protect patients, staff, and Protected Health Information.
What does HIPAA require for physical access control in hospitals?
HIPAA's Security Rule requires covered entities to implement physical safeguards limiting access to systems containing PHI, including workstation controls, facility access procedures, and access logging. The goal is ensuring only authorized personnel can reach sensitive data or the spaces where it resides — with four addressable implementation specifications covering contingency operations, facility security plans, access control and validation, and maintenance records.
What is role-based access control (RBAC) in a hospital?
RBAC assigns access permissions based on job function rather than per individual. A pharmacist can access the medication room while a receptionist cannot. This simplifies permission management, reduces over-permissioning, and makes audits or revocations straightforward — particularly when integrated with HR systems that update permissions automatically as roles change.
Which hospital areas require the strictest access control?
The highest-risk zones typically requiring multi-factor or biometric access include pharmacies and medication storage, server rooms and data centers, ICUs and NICUs, psychiatric and behavioral health wards, operating rooms, and any area where PHI is physically accessible.
How does biometric access control improve hospital security compared to key cards?
Biometric credentials are bound to the individual and cannot be lost, shared, forgotten, or stolen — unlike key cards or PINs. Contactless biometric options such as palm vein scanning also support hygiene requirements in clinical settings by eliminating shared-touch surfaces. This makes them the highest-assurance credential option for sensitive hospital zones where accountability and infection control both matter.