Introduction
Banks are the most lucrative target for cybercriminals—and the numbers reflect it. The average cost of a data breach in the financial sector reached $6.08 million in 2024—22% higher than the global average. For the fourth consecutive year, finance and insurance ranked as the second most attacked industry, accounting for 23% of incidents.
Passwords, SMS OTPs, and mobile-only authentication have not kept pace. Each of these methods has proven vulnerable to phishing, SIM swapping, and credential theft at scale.
Hardware authentication has evolved from simple one-time password tokens into a broad ecosystem that includes FIDO2 keys, smart cards, and biometric devices. Choosing the right approach is both a security imperative and a regulatory requirement.
This guide covers what hardware authentication is, the threats driving its adoption, the main device types, compliance implications, and how to evaluate the right solution for your institution.
TLDR
- Hardware authentication uses a physical device to verify identity, making it far harder to compromise than passwords or SMS codes alone
- Banks face trojans, phishing, credential stuffing, SIM swapping, and nation-state attacks targeting mobile and software-based authentication
- Common types include FIDO2 security keys, OTP tokens, smart cards, and biometric devices — each with different security and compliance trade-offs
- PSD2/PSD3, GLBA, FFIEC, and 23 NYCRR 500 all push banks toward multi-method, hardware-backed authentication
- The strongest solutions are phishing-resistant, include liveness detection, cannot be shared or stolen, and operate independently of mobile networks
What Is Hardware Authentication for Banks?
Hardware authentication verifies identity using a physical device—the "something you have" factor. This fits into the three pillars of authentication in cybersecurity:
- Knowledge — password or PIN
- Possession — physical token or smart card
- Inherence — biometrics such as palm vein or fingerprint
Banking-grade security increasingly demands two or all three of these factors combined to create defense-in-depth against modern threats.
In practice, hardware authentication devices work through cryptographic operations performed within the device itself. A physical token generates a cryptographic code, stores a private key, or captures a biometric reading that the authentication system validates. No secrets are transmitted during this exchange. The private key never leaves the device, which makes remote compromise practically impossible.
The core difference between hardware and software-based MFA is the attack surface. Software solutions — app-based OTPs, SMS codes — operate within the same environment as the device being protected. If malware hits that device, the authentication layer falls with it. Hardware tokens operate independently of the host device, so they hold up against malware, SIM swapping, and the device-level compromises that routinely defeat software-only approaches.
Why Banks Are Prime Targets: The Threat Landscape
Financial institutions hold the highest-value combination of sensitive personal data and direct access to money, making them the top target for cybercriminals. The average cost of a data breach in finance isn't just a statistic—it quantifies real financial exposure from credential theft, account takeover, and fraud losses that hardware authentication directly prevents.
Banks face specific attack vectors that exploit mobile and software authentication weaknesses:
- Banking trojans like QakBot steal credentials silently, delivered via phishing campaigns that install malware capable of silently monitoring active banking sessions
- SIM swapping attacks resulted in $25,983,946 in reported losses in 2024, hijacking SMS OTPs by transferring phone numbers to attacker-controlled devices
- Adversary-in-the-Middle (AiTM) phishing kits harvest session cookies to bypass MFA entirely — intercepting authentication tokens even when users complete the MFA step correctly

Nation-state threats expose a deeper vulnerability. In October 2024, Chinese state-sponsored hackers infiltrated US telecommunications companies, showing how coordinated attacks against mobile infrastructure can render mobile-only authentication useless at scale. Hardware tokens operate independently of mobile networks and aren't affected by these disruptions.
Physical access threats are often overlooked. Unsecured workstations, branch terminals, and server rooms become attack vectors without hardware-based local authentication controls.
Banking security requires unified physical and digital protection. Hardware authentication addresses both layers in a single deployment.
Legacy software workarounds fail consistently. SMS OTPs are interceptable, app-based authenticators can be bypassed if a device is compromised, and passwords are routinely stolen via phishing. The common thread: any authentication method running on a general-purpose device shares its attack surface with threats on that device.
Types of Hardware Authentication for Financial Institutions
FIDO2 Security Keys
FIDO2 security keys represent phishing-resistant hardware tokens that use public-key cryptography. The private key never leaves the device, authentication codes are bound to the specific website or application, and they connect via USB, NFC, or Bluetooth. This design prevents phishing because even if a user is tricked into visiting a fake banking site, the FIDO2 key won't authenticate—it only responds to the legitimate domain.
Key trade-offs to understand:
- Strengths: Modern browser and platform compatibility, high security, relatively low cost
- Limitation: Not inherently PSD2/PSD3 compliant — FIDO2 keys authenticate the user but don't cryptographically bind transaction details, which dynamic linking requires
By 2027, more than 90% of MFA transactions using a token will be based on FIDO authentication protocols, making them a dominant standard for web authentication.
OTP Hardware Tokens
OTP and TOTP tokens generate single-use codes displayed on a screen that users enter manually during login. The key distinction lies between simple single-button authenticators (one factor only, vulnerable to phishing if the code is entered on a fake site) and OTP calculators with PIN and display that are capable of PSD2 compliance via dynamic linking.
RFC 6238 defines the Time-Based One-Time Password Algorithm, where codes rotate every 30-60 seconds based on synchronized time. While this prevents replay attacks, manual code entry creates friction and phishing vulnerability remains a weakness—attackers can capture codes in real-time and use them immediately.
Smart Cards with Certificate-Based Authentication
Smart cards store X.509 digital certificates and perform cryptographic operations on-chip, requiring a PIN and a card reader. NIST SP 800-73-4 defines interfaces for Personal Identity Verification smart cards used in government and high-security applications.
The private key is generated and stored in tamper-resistant hardware, making smart cards phishing-resistant and highly secure. The practical drawbacks, however, are significant:
- Card readers required at every workstation
- Full PKI infrastructure needed for certificate management
- Not inherently PSD3-compliant
These requirements make smart cards less practical for customer-facing banking deployments, though they remain a strong fit for employee and privileged access use cases.
Biometric Hardware Authentication
Biometric hardware authentication eliminates the core vulnerability of every token-based method: the credential can't be borrowed, stolen, or forgotten, because it's part of the person. Rather than relying on something you carry, it verifies an immutable physical characteristic — a fingerprint, palm vein pattern, or iris — that exists nowhere else.
Palm vein scanning, the technology at the core of ePortID's solution (developed in partnership with Fujitsu), scans subcutaneous (under-skin) vein patterns using near-infrared light.
The Fujitsu F-Pro scanner creates an identity derived from 5 million unique data points that cannot be replicated even between identical twins. Verification completes in under 2 seconds with 99.99991% accuracy. Critically, the system includes liveness detection—emitting infrared light to verify the vein pattern exists beneath living skin, defeating spoofing attempts with photographs, replicas, or silicone molds.
Biometric hardware contrasts fundamentally with token-based methods. Tokens rely on the "possession" factor and can be transferred to another person. Biometrics rely on the "inherence" factor — permanently tied to the individual — eliminating buddy-punching, shared credentials, and the ongoing logistics of token distribution and replacement.

ePortID brings this technology to financial institutions with a track record built across high-security environments, including deployments for the US Navy, military joint task forces, port authorities, and commercial clients such as Fiserv.
Key Benefits of Hardware Authentication Over Software-Only Approaches
Hardware authentication outperforms software-only approaches across four areas that matter most to banks: threat resistance, operational resilience, compliance, and user experience.
Phishing and malware resistance is built into how hardware works. Cryptographic operations happen inside the device — private keys never touch the host system. An attacker who installs malware on a workstation or intercepts traffic still can't forge authentication without the physical device present. In biometric systems, the enrolled individual must also be physically there. CISA explicitly recommends FIDO/WebAuthn and PKI-based MFA as the gold standard for phishing-resistant authentication.
Network and OS independence removes a common failure point. Hardware tokens function without cellular connectivity, internet access, or a working mobile OS. This matters when:
- Network jamming or carrier outages disrupt SMS-based authentication
- SIM swapping compromises mobile credentials
- Nation-state actors target telecommunications infrastructure during coordinated attacks
Auditability and non-repudiation tie access to a physical device or biometric identity — not a shareable credential. Authentication is timestamped, logged, and indisputable. Hardware authentication systems create complete audit trails with entry, exit, and duration tracking, plus real-time alerts for denied access attempts or unusual patterns. This satisfies regulatory requirements and supports fraud investigations with hard evidence.
Operational efficiency improves measurably. Biometric authentication eliminates passwords, separate token devices, and manual code entry. Contactless palm vein scanning completes in under 2 seconds with no physical contact. Forrester Research found that each password reset costs $70 — hardware authentication removes that cost from the budget entirely.
Compliance Requirements Banks Must Meet
US Regulations:
Key US rules shaping hardware authentication requirements:
- GLBA Safeguards Rule — Requires MFA for anyone accessing customer information; May 2024 amendments expanded MFA scope and tightened data security plan requirements.
- FFIEC Authentication Guidance — Specifies that where single-factor authentication is inadequate, MFA or controls of equivalent strength must be part of layered security.
- 23 NYCRR 500 (New York DFS) — Mandates MFA for remote access to information systems, third-party cloud applications, and all privileged accounts except service accounts that prohibit interactive login.
EU and Global Standards:
- PSD2 / SCA with Dynamic Linking — Authentication codes must be specific to the transaction amount and payee. Simple FIDO2 keys and basic OTP tokens don't meet this bar without additional capabilities.
- PSR (PSD2 successor) — Provisional agreement reached November 2025; explicitly bans mobile-only SCA and requires support for diverse authentication mechanisms including hardware devices.
- PCI DSS v4.0 — Extends MFA to all access into the cardholder data environment, not just administrative access, requiring hardware authentication for significantly broader user populations.
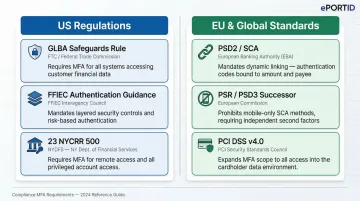
The compliance case extends beyond avoiding penalties. Hardware authentication simplifies audit processes, reduces the attack surface regulators scrutinize, and positions institutions ahead of tightening requirements. Organizations deploying hardware auth meet these standards directly — without relying on layered compensating controls.
What to Look for in a Bank-Grade Hardware Authentication Solution
Start with phishing resistance and liveness detection — both are non-negotiable. Any hardware authentication solution for a bank should be built on phishing-resistant protocols such as FIDO2 or certificate-based authentication. For biometric solutions, liveness detection prevents spoofing with photographs, video, or replicas. NIST SP 800-63B defines Authenticator Assurance Level 3 (AAL3) as requiring hardware-based authenticators with verifier impersonation resistance — the highest assurance level available.
On the operational side, prioritize independence, durability, and zero-footprint design. The device should require no software installation on host systems, function without internet or cellular connectivity, and hold up under daily institutional use. Experience in high-security environments matters here — ePortID's 20 years serving the US Navy, military joint task forces, and port authorities translates directly into the reliability financial institutions demand.
That operational track record also shapes how well a solution handles the third dimension: scalability and integration.
Evaluate whether the solution integrates with existing IAM/SSO infrastructure through standards like LDAP, Active Directory, or SAML. A single credential covering both physical access (branch doors) and logical access (network logins) eliminates duplicate systems — and duplicate costs. Measurable ROI should follow quickly:
- Replaces multiple authentication mechanisms with one unified system
- Eliminates password reset costs ($70 per reset on average)
- Reduces fraud losses through stronger identity assurance
- Pays for itself within months, not years
Microsoft research shows multifactor authentication reduces identity attack compromise risk by 99.9% — a figure that makes the business case straightforward.

Frequently Asked Questions
What is hardware authentication?
Hardware authentication is the use of a physical device to verify a user's identity, typically as part of multi-factor authentication. It operates independently of the system being accessed, making it resistant to malware and remote attacks that can compromise software-only methods.
What authentication do banks use?
Banks use a combination of methods: passwords/PINs, SMS OTPs, app-based authenticators, hardware tokens (FIDO2 keys, smart cards, OTP generators), and biometric authentication. Regulatory pressure is pushing institutions toward hardware-backed MFA specifically because it resists phishing and account takeover attacks.
What are the three types of authentication in cyber security?
The three authentication factors are:
- Knowledge — something you know, such as a password or PIN
- Possession — something you have, such as a hardware token or smart card
- Inherence — something you are, such as a fingerprint or palm vein scan
Strong authentication for banks typically combines at least two of these factors.
Are HSM and TPM the same?
HSMs (Hardware Security Modules) and TPMs (Trusted Platform Modules) are both hardware security devices but serve different purposes. HSMs are dedicated cryptographic processors used for key management at scale in banking infrastructure. TPMs are chips embedded in individual computers, handling device-level security only.
Which is better, SSO or MFA?
SSO and MFA are complementary rather than competing. SSO simplifies user experience by allowing one login to access multiple systems, while MFA adds security layers to that login. The strongest approach for banks combines both, using MFA (ideally hardware-backed) as the authentication mechanism that gates SSO access.