Introduction
Passwords were invented in the 1960s for university computers, when a single mainframe served a few hundred users and the biggest security threat was an unauthorized student checking class schedules. Today, financial institutions rely on that same 60-year-old technology to protect billions of daily transactions against credential-stuffing operations, AI-powered deepfakes, and phishing kits available for purchase on the dark web.
The structural problem is simple: passwords are shared secrets. The credential exists both on your device and on the bank's servers, creating multiple points of interception and compromise. IBM's 2024 X-Force Threat Intelligence Index found that stolen credentials now represent 30% of all cyber incidents, with usage surging 71% year-over-year. The financial sector remains a primary target—the Anti-Phishing Working Group reports that financial and payment sectors faced 30.9% of all phishing attacks in Q1 2025.
Those numbers make one thing clear: the password problem isn't a user behavior issue — it's an architectural one. This article breaks down why passwords keep failing financial institutions, what passwordless alternatives actually work, and how to make the transition compliantly.
TLDR
- Account takeover attacks cost consumers $15.6 billion in 2024, driven by stolen passwords and phishing
- FIDO passkeys eliminate phishing by replacing shared secrets with cryptographic key pairs that never leave the user's device
- Palm vein biometrics deliver the strongest authentication — credentials can't be lost, stolen, shared, or forgotten
- Liveness detection prevents spoofing and deepfake-based fraud in biometric systems
- Passwordless authentication reduces support costs, strengthens compliance, and improves customer retention
Why Passwords Are Failing Financial Institutions
Passwords operate on a "shared secret" model—the same credential lives on the user's device and on the institution's servers. This creates multiple attack surfaces: the credential can be phished during login, intercepted in transit, leaked from a database breach, or stolen via SIM swapping. Contrast this with cryptographic authentication, where a private key never leaves the user's device and no shared secret exists on a server to steal. That architectural flaw is what attackers exploit — repeatedly and at scale.
The Attack Vectors Banks Face Every Day
Financial institutions face a consistent stream of credential-based attacks:
- Phishing: Real-time phishing kits sold on the dark web can intercept credentials as users enter them, bypassing even SMS one-time passwords. The median time for users to fall for phishing emails is less than 60 seconds.
- Credential stuffing: Attackers use leaked password databases from other breaches to systematically test credentials against banking sites. Verizon's 2025 Data Breach Investigations Report found that credential stuffing accounted for 22% of initial access vectors.
- SIM swapping: Hijacking phone numbers to intercept SMS OTPs. The FBI's 2025 Internet Crime Complaint Center report recorded 971 SIM swap complaints with $25.9 million in reported losses, though the true impact is far higher as many incidents are categorized under broader account takeover fraud.
- Brute force: Automated attempts to guess weak passwords.

Account takeover (ATO) is the real-world consequence. Javelin Strategy & Research's 2025 Identity Fraud Study found that ATO fraud cost victims almost $16 billion in 2024, impacting 5.1 million consumers. Average losses reached $2,575 per victim. Attackers drain accounts, bypass SMS alerts, and exploit the window between credential capture and detection.
Consider a typical scenario: A customer receives what appears to be a legitimate text from their bank about suspicious activity. They click the link, enter their credentials on a spoofed site, and the attacker now has real-time access. Within minutes, funds are transferred to mule accounts, account recovery details are changed, and the customer is locked out—often before alerts even trigger.
The Hidden Operational Costs
Beyond direct fraud losses, passwords impose a significant operational tax. Gartner estimates that 20% to 50% of all IT help desk calls are for password resets, with Forrester calculating the average cost per reset at approximately $70.
Password friction also drives customer attrition. In a 2022 study, Signicat found that 68% of consumers had completely abandoned an onboarding application — up from 63% in 2020 — largely due to processes taking too long or demanding too much information.
McKinsey notes that customers don't switch banks for slightly better experiences. They switch because they're frustrated with their current provider's friction.
Passwordless Authentication Methods Financial Institutions Should Know
Passwordless authentication replaces the "something you know" factor — passwords — with two stronger alternatives: "something you have" (a device or token) and "something you are" (biometrics). The result isn't weaker security. Each method relies on cryptographic verification that passwords simply can't match.
FIDO Passkeys and Public Key Cryptography
FIDO2 passkeys work through asymmetric cryptography. At enrollment, a unique cryptographic key pair is generated—the private key never leaves the user's device, while the public key is stored on the bank's server. During authentication, the server sends a challenge that only the private key can sign. Because no shared secret is transmitted, phishing becomes structurally impossible—there is nothing to intercept.
WebAuthn binds credentials to specific domains, verifying that the origin matches the bank's actual domain. Even if a user visits a spoofed website, the authenticator will not release the credential.
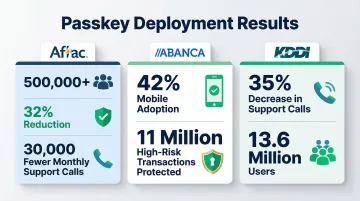
Proven ROI from early adopters:
- Aflac: 500,000+ enrolled customers, 32% reduction in password recovery requests, 30,000 fewer monthly support calls
- ABANCA: 42% mobile user adoption, 11 million high-risk transactions protected without technical incidents
- KDDI: Nearly 35% decrease in calls to customer support across 13.6 million users
Risk-Based and Adaptive Authentication
Risk-based authentication (RBA) assigns a dynamic trust score to each login attempt based on contextual signals:
- Device identity and registration status
- Geolocation relative to the user's typical access patterns
- Behavioral signals such as typing cadence or navigation habits
- Time of access against historical norms
Low-risk sessions proceed invisibly. When signals fall outside expected patterns, RBA triggers step-up authentication — adding friction only where the risk warrants it.
Push Notifications and Device-Bound Authentication
Push notification authentication outperforms SMS OTPs on every security dimension: encrypted end-to-end, immune to SIM swapping, and channel-bound to a trusted registered device. Regulators globally are deprecating SMS OTPs due to their vulnerabilities. Singapore's Monetary Authority announced in July 2024 that major retail banks will progressively phase out OTPs for bank account login. The UAE Central Bank's Notice 2025/3057 mandates the phase-out of SMS and email OTPs by March 31, 2026, shifting fraud liability to institutions that continue using these methods.
That regulatory direction raises a practical question: if SMS OTPs are out, what exactly replaces them — and how does passwordless fit into existing MFA frameworks?
Multi-Factor vs. Passwordless: Clarifying the Relationship
A common misconception: passwordless authentication is not the absence of security layers—it's MFA without passwords. Each method carries a different security profile, which matters when matching authentication to transaction risk:
| Method | Phishing Resistance | Key Dependency |
|---|---|---|
| Passkeys | Highest — cryptographically bound to domain | Requires enrolled device |
| Push notifications | Strong — channel-bound, encrypted | Requires registered device |
| Biometrics | Cannot be shared or stolen | Requires capable hardware |

For retail banking login, passkeys or biometrics provide appropriate security. For high-value wire transfers, institutions might combine biometrics with transaction-specific push notification approval.
Why Biometric Authentication Is the Strongest Security Layer
No other authentication method closes as many attack surfaces at once. Passwords can be phished, tokens can be stolen, and PINs can be shoulder-surfed — but biometrics cannot be lost, forgotten, shared, duplicated, or stolen. For financial institutions where credential theft translates directly to fraud exposure, that distinction matters.
Liveness Detection: The Essential Safeguard Against Spoofing
Liveness detection verifies that a biometric scan comes from a live human, not a photo, mask, or deepfake. Without liveness detection, a biometric system can be defeated by a high-resolution photograph. AI-powered liveness checks defend against increasingly sophisticated synthetic media attacks.
Sumsub's Identity Fraud Report 2025-2026 highlights 180% year-over-year growth in sophisticated fraud attacks, with deepfakes accounting for 11% of first-party fraud schemes. The IBM X-Force Threat Intelligence Index 2026 warns that attackers are using AI to speed research and iterate on attack paths in real time, including AI-driven image manipulation for synthetic identities.
NIST SP 800-63B explicitly states that biometric systems should implement Presentation Attack Detection (PAD) demonstrating at least 90% resistance to presentation attacks in accordance with ISO/IEC 30107-3.
Why Palm Vein Biometrics Outperform Face and Fingerprint for Banking
Among biometrics that also satisfy liveness requirements, palm vein scanning stands apart. It uses near-infrared light to map the vascular pattern beneath the skin. That pattern is derived from 5 million data points, unique to every individual — including identical twins — and cannot be replicated from the outside.
Key advantages over other biometric options:
- Immune to deepfake attacks and free from camera privacy concerns that complicate facial recognition deployments
- Contactless and hygienic — unaffected by surface damage like cuts or calluses that reduce fingerprint reliability
- Internal vascular patterns cannot be lifted, molded, or synthesized from external sources
ePortID's contactless palm vein solution, built on Fujitsu's PalmSecure technology, delivers 99.99991% accuracy with sub-2-second verification. Liveness detection is built in — the infrared scanner confirms active blood flow during every scan, with no separate step required.
The system has been deployed in high-security financial and infrastructure environments. Clients include Fiserv in financial services, along with critical infrastructure operators such as Tata Steel and Thyssen Krupp.
Accuracy at Scale: Why Precision Matters for Financial Institutions
Biometric accuracy rates are critical for banks operating at millions of transactions per day. Two metrics define performance:
- False Acceptance Rate (FAR): The probability the system incorrectly authenticates an unauthorized user
- False Rejection Rate (FRR): The probability the system incorrectly rejects an authorized user
NIST SP 800-63B sets a baseline FAR of 1 in 10,000 (0.01%) and FRR below 5.0% for biometric systems used in multi-factor authentication.
Fujitsu's PalmSecure technology demonstrates a FAR of under 0.00001% and FRR of 1.0%, significantly exceeding NIST's baseline. Because palm vein recognition relies on internal vascular patterns rather than external physical traits, it bypasses the vulnerabilities of facial recognition (deepfakes) and fingerprint scanners (latent prints/molds).

Real-World Use Cases: Passwordless Authentication in Banking
Use Case 1: Customer Login to Mobile and Online Banking
A returning customer opens their mobile banking app. Device recognition confirms the phone is trusted. The customer places their palm over the integrated scanner—verification completes in under 2 seconds with no password entry. Risk-based authentication handles edge cases: if the customer logs in from a new device or unusual location, the system triggers step-up verification through a push notification to the registered device, adding a security check that stops bad actors while letting legitimate customers through without friction.
Use Case 2: Authorizing High-Value Transactions
When a customer initiates a large wire transfer or adds a new payee, the bank prompts biometric authentication to confirm transaction details. The customer places their palm on the scanner to verify identity and consent. This creates a tamper-evident, cryptographically secure record of authorization that protects against social engineering attacks and internal fraud, with an audit trail ready for compliance reviews.
Use Case 3: Securing Employee and Branch Access
Bank employees accessing core banking systems, server rooms, and data centers represent an equally critical attack surface. The same biometric technology used for customer authentication can control employee access to sensitive internal systems, reducing insider threats and closing the door on compromised staff credentials.
ePortID's solutions integrate with existing access control infrastructure through Wiegand or OSDP protocols, so financial institutions can add biometric authentication without replacing their entire security architecture. The system delivers:
- Complete entry audit trails with entry, exit, and duration tracking
- Real-time alerts for denied entry attempts and unusual access patterns
The Business Case for Going Passwordless
Direct Cost Reductions
Financial institutions spend heavily on password infrastructure. With 20% to 50% of help desk calls related to password resets at $70 per incident, plus SMS OTP delivery fees at scale, the operational burden is substantial. Aflac's passkey deployment eliminated 30,000 monthly support calls. Account takeover losses add another $15.6 billion annually across the industry.
Regulatory Compliance Dividend
Passwordless biometric authentication aligns with a growing set of global mandates. Financial institutions operating across multiple markets are increasingly expected to meet:
- UAE Central Bank Notice 2025/3057
- Singapore MAS directives
- Philippines BSP Circular 1213
- PSD2 Strong Customer Authentication requirements (Europe)
- NIST 800-63 frameworks (US)

Building to these standards now means compliance is a byproduct of good architecture — not an emergency retrofit.
Competitive Differentiation
Compliance sets the floor; differentiation determines who wins customer loyalty. Banks that offer fast, password-free authentication reduce friction at the highest-dropout moments of the customer journey — login, transaction confirmation, and onboarding. McKinsey notes that customers switch banks due to frustration with friction, making superior authentication a direct driver of customer retention and lifetime value.
Frequently Asked Questions
What is passwordless authentication for banks?
Passwordless authentication replaces passwords with secure digital credentials, biometrics, or device-bound tokens, letting customers and employees verify identity securely without memorizing or transmitting a password.
Why are passwords no longer secure enough for financial institutions?
Passwords can be phished, stuffed from breach databases, intercepted via SIM swapping, and exploited through social engineering, making them fundamentally unsuited to the security risks banks face today. The shared-secret model leaves multiple openings that attackers consistently exploit.
What is the most secure biometric method for banking authentication?
Palm vein scanning is considered the most accurate and secure biometric for financial applications, offering near-zero false acceptance rates, contactless operation, built-in liveness detection, and a vascular pattern that cannot be replicated externally or compromised through surface damage.
Can biometric authentication be spoofed or hacked?
Modern biometric systems with active liveness detection are highly resistant to spoofing. Attacks using photos, masks, or deepfakes are defeated by liveness checks that confirm real human presence, such as detecting active blood flow in palm vein systems during authentication.
How does passwordless authentication help financial institutions meet compliance requirements?
Passwordless biometric authentication aligns with global regulatory mandates including UAE Central Bank directives, Singapore MAS guidelines, PSD2 Strong Customer Authentication, and NIST digital identity standards, making compliance a byproduct of strong security rather than a separate effort.
How long does it take to implement passwordless authentication at a financial institution?
Implementation timelines vary by institution size and existing infrastructure, but phased rollouts starting with high-risk use cases — employee access to core banking systems or high-value transaction authorization — typically deliver measurable security improvements within months. Systems that use Power-over-Ethernet architecture and integrate with existing access management infrastructure through standard protocols can further reduce both deployment complexity and installation time.