Introduction
Time theft isn't a minor HR headache—it's a $450 billion to $550 billion annual drain on U.S. businesses. According to the American Payroll Association, approximately 75% of U.S. employers experience losses related to time theft and buddy punching, with the average employee stealing roughly 4 hours and 5 minutes every week. From manufacturing floors where buddy punching inflates payroll by 2.2% of gross wages, to healthcare facilities where accurate time records are a compliance requirement, traditional timekeeping methods leave organizations vulnerable to fraud at every shift change.
This guide covers what you need to make an informed decision:
- How biometric time clocks eliminate time theft at the source
- Why biometric technologies differ in accuracy, hygiene, and reliability
- Which environments benefit most from contactless palm vein scanning
- What state-level compliance obligations apply to your deployment
- How to calculate ROI based on workforce size and current fraud exposure
TLDR
- Time theft drains payroll budgets silently—buddy punching alone costs employers 2.2% of gross payroll annually
- PINs, swipe cards, and paper logs verify credentials, not people, so fraud is structurally inevitable
- Biometric clocks authenticate physical identity, making buddy punching and credential sharing physically impossible
- Palm vein scanning delivers the highest accuracy, is fully contactless, and includes intrinsic liveness detection fingerprint and facial systems cannot match
- Compliance varies by state: Illinois, Texas, and Washington each impose specific notice and consent obligations before deployment
What Time Theft Really Costs Your Organization
Time theft takes five primary forms, each difficult to detect manually:
- Buddy punching — one employee clocks in for an absent colleague
- Timesheet inflation — rounding start times earlier or end times later
- Extended breaks — adding 10-15 minutes to lunch or break periods daily
- Personal tasks on the clock — handling errands, browsing social media, or taking extended personal calls during paid time
- Unscheduled stops — off-site employees making personal stops between job sites without clocking out
Time theft costs U.S. businesses between $450 billion and $550 billion annually, with the average cost reaching $11,000 per employee per year across all forms combined. For manufacturing operations, time theft can consume up to 7% of gross annual payroll.
In a 200-employee facility paying an average of $22 per hour, even a conservative 2% payroll leakage translates to over $180,000 in unearned wages paid annually.
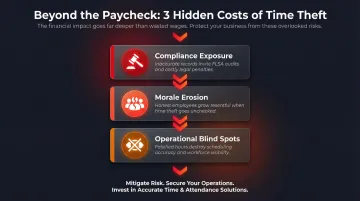
Beyond direct payroll loss, time theft creates three downstream consequences organizations often overlook:
- Compliance exposure — Falsified records create wage and hour audit risk under FLSA provisions, since overtime calculations built on fraudulent clock-ins can trigger regulatory penalties.
- Morale erosion — When honest employees watch peers game the system without consequence, resentment builds and high performers lose motivation.
- Operational blind spots — Managers who can't trust attendance data lose visibility into labor costs and scheduling accuracy, making it impossible to optimize staffing or spot process bottlenecks.
Why Traditional Time Clocks Fail to Stop Time Theft
The fundamental weakness of PIN codes, swipe cards, and key fobs is simple: they verify the credential, not the person. Each method has a built-in vulnerability:
- PIN codes can be shared verbally in seconds
- RFID badges fit in any wallet and pass between coworkers before a shift starts
- Key fobs can be handed off in a parking lot with no record of who actually used them
None of these methods confirm the person holding the credential is the employee on the clock.
Paper-based systems and manual sign-in sheets create records without verification. An employee signature on a timesheet confirms someone wrote a name and time — nothing more.
Supervisors monitoring sign-ins across busy facilities face a real problem during shift changes, when dozens of workers arrive at once across multiple entry points. No manual process can keep pace with that volume, which is exactly when buddy punching goes undetected.
The costs of maintaining traditional methods add up faster than most organizations realize. Password and PIN resets cost an average of $70 each in IT and administrative time, while replacing lost or damaged ID badges runs roughly $25 per instance. Across a workforce of 500 employees, even modest monthly replacement and reset volumes generate thousands in administrative overhead—costs typically buried in general admin budgets rather than attributed to time fraud prevention.
How Biometric Time Clocks Eliminate Time Theft
Biometric systems authenticate the individual, not something they carry or remember. This shifts verification from credential-based (what you have or know) to identity-based (who you are). The distinction eliminates the structural vulnerability that makes traditional systems exploitable.
Buddy Punching Becomes Physically Impossible
When a biometric clock requires a fingerprint, palm scan, or facial recognition to record attendance, the actual employee must be physically present. There's no badge to hand off, no PIN to share. Research shows eliminating buddy punching saves companies an average of 2.2% of gross payroll — a figure that translates directly to measurable ROI.
Real-Time Attendance Visibility
Biometric systems generate tamper-resistant, timestamped records the moment a scan occurs. Managers see who arrived, when, and for how long — without manual entry or reconciliation. The data flows directly into payroll systems, eliminating the lag and transcription errors that plague paper logs and spreadsheet-based tracking.
Payroll Accuracy and Downstream Savings
Clean time data eliminates disputed hours, correction cycles, and compliance exposure. IDC analyst data shows biometric time clock deployments delivering 537% ROI, with average payback periods of just 4.2 months.
The per-organization savings add up fast. For every 100 users, companies typically recover:
- $59,250 annually through eliminated buddy punching and reduced overpayments
- 75–200 hours of HR staff time per year previously spent on manual data entry
- Fewer dispute resolution cycles and compliance corrections

Liveness Detection as an Additional Fraud Layer
Advanced biometric systems check for "liveness" during verification — confirming the scan comes from a living person, not a photo, cast, or replica. This addresses spoofing attempts directly.
Systems using vascular biometrics, such as palm vein scanning, have intrinsic liveness detection. The sensor only recognizes patterns when deoxygenated blood is actively flowing through veins beneath the skin — making a spoof essentially impossible without a live hand present.
Not All Biometric Clocks Are Equal: Comparing Technologies
Four biometric modalities dominate the time and attendance market, each with distinct accuracy, hygiene, and environmental characteristics:
Fingerprint scanners capture surface-level ridge patterns on fingertips. They're familiar to most users and relatively affordable, making them common in general office environments. However, fingerprint accuracy degrades significantly with wet, dirty, or aging hands—conditions prevalent in manufacturing, warehousing, and industrial settings. Contact-based fingerprint scanners also introduce hygiene concerns, particularly in healthcare and food manufacturing, where scanner surfaces can act as vectors for pathogen transmission.
Facial recognition systems use cameras to map facial geometry. They offer high throughput at entry points because users don't need to stop or touch anything. However, accuracy varies with lighting conditions, facial coverings (masks), and camera angles. Without advanced presentation attack detection (PAD), facial systems remain vulnerable to photos, video replays, and 3D printed masks.
Iris scanning analyzes the unique patterns in the colored ring around the pupil. It delivers high accuracy and is contactless, but requires precise alignment and controlled lighting. Users must position themselves carefully within the scanner's field of view, which can slow throughput in high-traffic environments.
Palm vein scanning captures the vascular pattern beneath the skin using near-infrared light. The biometric data point is internal, invisible to the naked eye, and impossible to lift from surfaces or photograph. ePortID's palm vein solution, powered in partnership with Fujitsu, maps 5 million data points, achieves 99.99991% accuracy, and verifies identity in under 2 seconds. The vascular pattern is unique to each individual—peer-reviewed studies confirm even identical twins have distinguishable vein patterns.

Accuracy and False Acceptance Rates Matter
The four modalities described above aren't equally reliable — and in high-security or high-volume environments, the gap matters. Palm vein technology delivers a false acceptance rate (FAR) below 0.00001%, meaning fewer than one in 10 million scans incorrectly grants access. Fingerprint systems typically achieve FAR around 0.001% — 100 times less accurate.
Why Contactless Palm Vein Scanning Leads in Accuracy and Hygiene
Unlike surface biometrics, palm vein systems store only an encrypted mathematical template derived from the vascular pattern — never an image. That template cannot be reverse-engineered into a usable scan, which fundamentally changes the data breach equation.
Independent iBeta testing confirms Fujitsu PalmSecure achieves a 0% presentation attack (spoofing) success rate, meaning no attempted spoof using photos, casts, or replicas succeeded during ISO/IEC 30107-3 Presentation Attack Detection (PAD) testing.
The "Can't Be Lost, Shared, or Stolen" Distinction
Fingerprints can be lifted from glass, metal, or plastic surfaces. Faces can be photographed. But palm vein patterns exist beneath the skin and require active blood flow to register. The encrypted template stored in the system cannot be reverse-engineered into the original scan, reducing data breach risk compared to surface biometrics.
Matching the Technology to the Environment
- Fingerprint: General office use, low-traffic environments, lower security requirements
- Facial recognition: Entry points with high throughput, minimal user interaction required
- Palm vein: Critical infrastructure, healthcare, financial institutions, manufacturing, ports, and high-security facilities where hygiene, spoofing resistance, and indisputable records are non-negotiable
Privacy, Legal Compliance, and Secure Data Handling
Modern biometric systems do not store images of fingerprints, faces, or palms. Instead, they convert unique measurements into an encrypted numerical template that cannot be reverse-engineered into the original scan. This substantially reduces data breach risk and addresses many privacy concerns at the architectural level.
Key Legal Frameworks to Know
Several U.S. states impose specific obligations on employers collecting biometric data. The table below summarizes the primary laws:
| Jurisdiction | Law | Core Requirements | Penalties |
|---|---|---|---|
| Illinois | BIPA | Written notice, employee consent, published retention schedule, data destruction within 3 years | $1,000 (negligent) / $5,000 (intentional) per violation |
| Texas | CUBI | Notice and consent before capture; prohibition on sale or disclosure | Up to $25,000 per violation, enforced by the Attorney General |
| Washington | RCW 19.375 | Notice and consent before enrolling biometric identifiers for commercial purposes | Civil action by the Attorney General |
For organizations operating outside the U.S., international rules add another layer. GDPR Article 9 classifies biometric data as a "special category," generally prohibited from processing unless the employee provides explicit consent or processing is required under employment law obligations. Member State safeguards apply.
Employer Responsibilities Before Deployment
Before rolling out a biometric system, organizations should:
- Update employee handbooks to include biometric data policies
- Provide written notice explaining what biometric data will be collected, why, and how long it will be retained
- Obtain written or electronic consent from employees
- Publish a data retention and deletion schedule
- Confirm the vendor uses industry-standard encryption (AES-256 or equivalent) both in transit and at rest
- Verify biometric templates are stored separately from other employee records
- Ensure audit trails and role-based access controls are in place
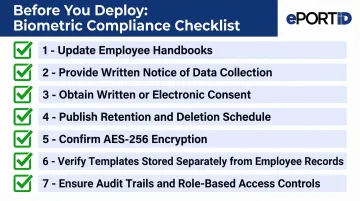
Vendors should provide clear documentation covering encryption standards, template storage practices, and audit trail capabilities — ask for this before signing any contract.
How to Choose and Implement the Right Biometric Clock
Before selecting a product, assess your organization's specific vulnerabilities. Key factors include:
- Number of sites and total workforce size
- Shift patterns and peak clock-in volumes
- Hygiene requirements (contactless vs. touch-based)
- Whether the system needs to double as an access control solution
A 50-employee office with salaried staff has different needs than a 500-employee warehouse running three shifts with high turnover.
Confirm that any biometric solution connects directly to your time-and-attendance, payroll, and scheduling platforms. Clock-in data should flow automatically into payroll runs—systems requiring manual export and import create new bottlenecks and reintroduce the very errors you're trying to eliminate.
High-security environments require an additional layer of scrutiny. Organizations in ports, energy, healthcare, defense, and financial services should prioritize contactless solutions with liveness detection and a documented track record in demanding conditions. ePortID has over 20 years of deployment experience with the U.S. Navy, Army JTF, Marine Corps, and Port Authorities, and serves commercial clients including Fiserv, Dow Chemical, Tata Steel, and Thyssen Krupp—organizations where security, hygiene, and compliance aren't optional.
Frequently Asked Questions
What is the most effective type of biometric clock for preventing time theft?
Palm vein scanning offers the highest accuracy among biometric options and is fully contactless. It resists spoofing, eliminates hygiene concerns, and produces audit-ready records — the right fit for environments where security and compliance are non-negotiable.
Can biometric time clocks be fooled or spoofed?
Systems with liveness detection cannot be spoofed by photographs, casts, or replicas—the clock confirms the scan comes from a living person. Palm vein biometrics scan a vascular pattern beneath the skin that cannot be replicated from external surfaces, achieving 0% spoof success in independent testing.
How does a biometric time clock prevent buddy punching?
Biometric clocks verify identity through a physical trait unique to each employee, not a card or PIN that can be passed to a colleague. Clocking in for an absent coworker is structurally impossible — the system requires that person to be physically present.
Are biometric time clocks legal to use in the workplace?
Biometric time clocks are legal in most U.S. jurisdictions, though compliance requirements vary by state. Illinois (BIPA), Texas (CUBI), and Washington each require employee consent and a published data retention policy before deployment.
How long does it take for a biometric time clock to pay for itself?
Most organizations recover their investment within 3 to 6 months. Independent research cites an average payback period of 4.2 months and 537% ROI, driven by payroll accuracy gains, lower administrative overhead, and eliminated buddy punching.
What industries benefit most from biometric time clocks?
Any industry with shift-based hourly workers, multi-site operations, or strict access control requirements benefits significantly. Manufacturing, logistics, healthcare, financial services, energy, and critical infrastructure sectors see particularly strong ROI due to high labor costs, compliance obligations, and security requirements.