Do I need a license to install access control in Texas?
Texas requires contractors installing access control systems as part of alarm or security system work to hold either an alarm systems contractor license or an alarm installer registration through the Texas Department of Public Safety Private Security Program. However, if the biometric access control installation is performed as a standalone service not integrated with monitored alarm systems, licensing requirements may differ. We recommend verifying current state regulations with the Texas DPS or consulting with your legal advisor. ePortID works with licensed contractors and can coordinate compliance requirements for your installation project to ensure all regulatory standards are met.
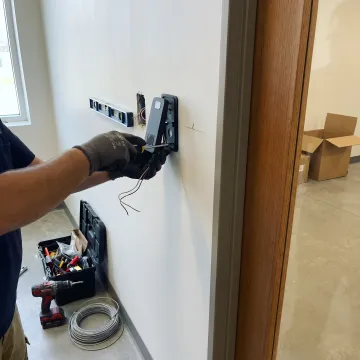
How long does biometric access control installation take?
Installation timelines vary based on facility size and complexity. A single-door installation with basic integration typically takes 4-6 hours including mounting, wiring, network configuration, and initial testing. Multi-door enterprise installations range from 2-5 business days depending on the number of access points, existing infrastructure integration requirements, and user enrollment scope. Critical infrastructure projects requiring TWIC verification or multi-factor authentication may require additional configuration time. We provide detailed project timelines during the site assessment phase and work flexible schedules to minimize operational disruption, including after-hours and weekend installation options.
What is the accuracy rate of palm vein biometric systems?
ePortID's Fujitsu PalmSecure technology delivers 99.99991% accuracy with a false acceptance rate of 0.00001% and false rejection rate of 0.01%. The system derives identity from 5 million unique data points within the palm's vein pattern—a pattern shared by no one else, not even identical twins. Verification completes in under 2 seconds while checking for liveness to prevent spoofing attempts. This contactless technology cannot be lost, shared, forgotten, duplicated, or stolen like cards or passwords. The system maintains accuracy across diverse user populations and environmental conditions, making it ideal for high-security applications where credential integrity is mission-critical.
Can biometric systems integrate with my existing access control infrastructure?
Yes, ePortID systems are designed for seamless integration with existing access control platforms without requiring complete system replacement. Our biometric readers interface via industry-standard Wiegand protocol (supporting any bit format) or OSDP (Open Supervised Device Protocol) to communicate with your current controllers, electric strikes, mag-locks, turnstiles, and gate systems. The installation preserves your existing management software, user databases, and reporting infrastructure while adding biometric authentication layers. For critical infrastructure requiring TWIC credential verification, our systems validate cards against TSA's real-time cancelled card list while generating standard control signals to your access hardware. This integration flexibility significantly reduces implementation costs and deployment time.
What are the ongoing maintenance requirements for biometric access control?
ePortID's contactless palm vein systems require minimal maintenance due to non-contact operation that eliminates wear from fingerprint residue or physical contact. Routine maintenance includes quarterly inspection of reader lenses for dust accumulation, verification of network connectivity, and software updates delivered remotely. The Fujitsu PalmSecure hardware includes a two-year manufacturer warranty covering defects. Unlike card-based systems, there are no credentials to replace when lost or damaged. User enrollment is a one-time process with permanent biometric templates stored securely. We provide comprehensive training for your administrators to manage user permissions, generate audit reports, and configure alerts. Optional maintenance contracts include priority technical support, annual system health checks, and guaranteed replacement hardware availability.
How secure is the biometric data collected by the system?
ePortID systems employ bank-level security protocols to protect biometric data. Palm vein patterns are captured and immediately converted into encrypted mathematical templates—the actual vein image is never stored. These templates cannot be reverse-engineered to recreate the original biometric data and are useless if intercepted. Data transmission between readers and servers uses AES-256 encryption over secure networks. For facilities requiring heightened security, templates can be stored locally on encrypted readers rather than centralized databases. The contactless palm vein technology itself provides inherent security advantages: it measures internal vein patterns invisible to the naked eye, checks for blood flow to prevent spoofing with photographs or models, and cannot be duplicated through social engineering or physical theft.
What happens during a power outage or network failure?
ePortID systems include multiple fail-safe mechanisms to maintain security during infrastructure disruptions. Readers can operate in offline mode using locally cached authentication data, allowing verified users to access facilities during network outages. Battery backup options maintain reader functionality during power failures for up to 8 hours depending on configuration. For critical access points, we recommend implementing uninterruptible power supplies (UPS) to ensure continuous operation. The system automatically logs all authentication attempts during offline operation and synchronizes transaction data once connectivity is restored, maintaining complete audit trails. Administrators can configure emergency access protocols that activate during extended outages while maintaining security integrity. We design redundancy into enterprise installations to prevent single points of failure.
Can the system accommodate visitors and temporary contractors?
Yes, ePortID systems excel at managing diverse user populations with flexible credential types. Visitors can be enrolled in minutes using rapid palm vein scanning at reception areas, with permissions automatically expiring after predetermined timeframes. Contractors receive time-bound, location-specific access credentials that activate and deactivate on scheduled dates without administrator intervention. The system supports multi-level authentication options: permanent employees might use biometric-only access, while visitors require biometric plus escort authorization. Real-time dashboards show all active temporary credentials and provide instant revocation capabilities. For high-traffic visitor environments, the system integrates with existing badge printing workflows to combine biometric enrollment with physical credential issuance. Audit trails track all visitor activity including entry, exit, duration, and escort assignments for comprehensive security reporting.