How much does access control cost per door?
Access control costs vary based on system complexity and authentication requirements. Basic single-door installations with contactless biometric readers typically start around $1,500-$2,500 per door, including hardware and installation. Systems requiring two or three-factor authentication (biometric plus card and/or PIN) may range from $2,500-$4,000 per door. Enterprise deployments with centralized management, real-time alerts, and audit trail capabilities require custom pricing based on door count, networking requirements, and integration with existing systems. Many clients find systems pay for themselves within 3-6 months through eliminated credential replacement costs and reduced unauthorized access incidents.
How much does it cost to install an automated gate?
Automated gate installation costs depend on gate type, biometric integration level, and vehicle/pedestrian requirements. Basic pedestrian gates with biometric access control range from $8,000-$15,000, including reader installation and controller integration. Vehicle gate systems with driver and passenger scanning capabilities typically range from $15,000-$35,000 depending on gate size, automation complexity, and whether TWIC verification or license plate recognition is required. High-security installations for critical infrastructure with redundant systems and real-time monitoring can exceed $50,000. We provide detailed site assessments to develop accurate quotes based on your specific security requirements and existing infrastructure.
What is a gate access control system?
A gate access control system manages entry authorization for pedestrian or vehicle gates using electronic verification. Modern biometric gate systems use contactless palm vein scanning to verify identity before granting access—eliminating cards or codes that can be shared or stolen. The system integrates a biometric reader, controller, and gate automation mechanism. When authorized users present their palm, the system verifies identity in under 2 seconds, checks permissions for that specific location and time, then sends a signal to open the gate. Complete audit trails log all access attempts with timestamps, and real-time alerts notify security of denied access or unusual patterns. Systems can integrate with existing gate hardware via standard protocols.
Can your access control system integrate with our existing security infrastructure?
Yes, ePortID systems integrate seamlessly with most existing access control platforms through industry-standard Wiegand and OSDP protocols. Our biometric readers can send authentication signals to your current gate controllers, turnstile systems, or door strike mechanisms without replacing core infrastructure. For facilities using access cards, we offer hybrid systems that combine biometric verification with card readers for two-factor authentication. Data integration is also straightforward—our systems can interface with your security management software, HR databases, and payroll systems via secure APIs. During site assessment, we evaluate your existing setup and design an integration approach that minimizes disruption while maximizing security improvements.
How secure is palm vein biometric technology compared to fingerprint or card systems?
Palm vein biometrics is significantly more secure than fingerprint scanning or access cards. The technology maps internal vein patterns beneath the skin using near-infrared light—creating a unique template from 5 million data points that can't be replicated even by identical twins. Unlike fingerprints which can be lifted and reproduced, palm veins are internal and invisible, making spoofing virtually impossible. The system actively checks for blood flow during each scan, preventing the use of fake hands or photographs. Accuracy reaches 99.99991% with false acceptance rates near zero. Access cards can be lost, shared, or stolen; palm vein patterns can't. This makes it ideal for high-security environments where credential integrity is critical.
What happens if an employee leaves the company? How quickly can access be revoked?
Access revocation is instantaneous across all connected locations. When an employee is terminated in our system, their biometric credentials are immediately deactivated network-wide—no need to collect cards or wait for IT to update multiple systems. The system maintains a complete audit trail, so if a former employee attempts access, you receive a real-time alert with timestamp and location. This is a significant advantage over card-based systems where terminated employees may retain physical credentials. For contractors or temporary workers, you can set time-bound permissions that automatically expire, and location-specific access that restricts certain individuals to designated areas only. All permission changes sync in real-time across your entire deployment.
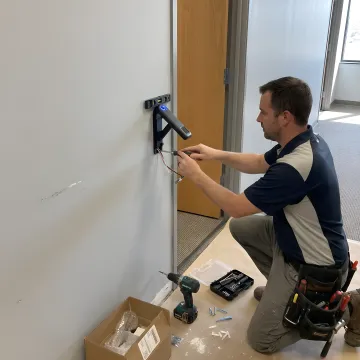
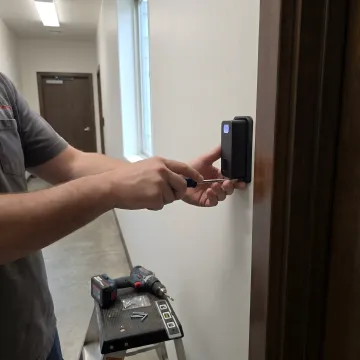
Is installation disruptive to our daily operations?
Installation is designed for minimal operational disruption. Most single-door installations take 2-4 hours and can be scheduled during off-hours or low-traffic periods. The biometric readers mount easily to existing door frames, turnstiles, or gates without extensive construction. Wiring integrates with current access control infrastructure in most cases. For enterprise deployments, we work in phases—installing and testing sections of your facility incrementally so business continues normally. User enrollment is streamlined: each person's palm vein pattern is captured in seconds, and the one-time enrollment works across all your access points. We provide on-site training to ensure your team is comfortable with the system before we complete the project.
Do you provide ongoing maintenance and support after installation?
Yes, we offer comprehensive maintenance and support packages tailored to your facility's requirements. Standard support includes remote system monitoring, software updates, troubleshooting assistance, and replacement of defective hardware covered under warranty. On-site service plans are available for facilities requiring rapid response times or regular preventive maintenance. Our support team has direct access to Fujitsu's engineering resources, ensuring technical issues are resolved quickly. We also provide user training refreshers, system optimization consultations, and capacity expansion planning as your needs evolve. Most clients choose annual support contracts that include priority response, quarterly system health checks, and unlimited technical support calls. Emergency support is available 24/7 for critical infrastructure applications.