Traditional passwords fail in high-security environments. They're phished, reused, brute-forced, and shared. In physical access settings, PIN codes enable buddy punching and leave no indisputable record of who actually entered a restricted space. Meanwhile, password resets consume 20-50% of help desk resources at an average cost of $70 per ticket.
This article defines passwordless authentication, walks through its main types, and makes the case for biometric verification—specifically contactless palm vein technology—as the most reliable path forward for critical infrastructure and enterprise security.
TLDR
- Passwordless authentication eliminates passwords, using biometrics, security keys, or one-time codes instead
- Biometrics verify identity through physical traits — ones that can't be lost, stolen, forgotten, or shared
- Palm vein scanning reaches 99.99991% accuracy in under 2 seconds — and checks for liveness to block spoofing attempts
- Phishing-resistant authentication removes the credential vulnerabilities that drive most enterprise breaches
- Most biometric deployments pay for themselves within 3 to 6 months through reduced help desk load and eliminated payroll fraud
What Is Passwordless Authentication and How Does It Work?
Passwordless authentication verifies identity without requiring a traditional password. Instead of typing credentials, users authenticate using factors tied to what they have (a device or security key), what they are (biometric traits), or where they are (location-based verification).
Authentication factors fall into three categories:
- Knowledge (something you know): Passwords, PINs, security questions
- Possession (something you have): Security keys, smartphones, one-time codes
- Inherence (something you are): Fingerprints, facial geometry, palm vein patterns
Passwordless systems eliminate the knowledge factor entirely. They rely only on possession and inherence — factors tied to physical objects or biology, not secrets that can be guessed, phished, or transmitted across a network.
Passwordless vs. MFA: What the Difference Actually Means
Traditional multi-factor authentication (MFA) adds a second verification step on top of a password. True passwordless authentication removes the password completely, relying only on possession and inherence factors.
"Passwordless MFA" combines two non-password factors — for example, a biometric scan paired with a trusted device — delivering the strongest available verification without any shared secret. CISA identifies this as "phishing-resistant MFA", the gold standard for enterprise and regulated environments. Only FIDO2/WebAuthn and PKI-based authentication meet this threshold.
How the Authentication Flow Works
The core passwordless login sequence operates through cryptographic challenge-response:
- User initiates login at a device or access point
- System issues a cryptographic challenge
- User's device or biometric scanner responds using a private key or biometric match
- Server verifies the response without any shared secret being transmitted
This public/private key exchange, the foundation of FIDO2 and passkey standards, is resistant by design to phishing and man-in-the-middle attacks. The credential never leaves the user's device. If a user visits a phishing site on a different domain, the authenticator won't present the credential.
The Problem with Passwords in High-Security Environments
Passwords create five critical vulnerabilities:
- Phishing: Users enter credentials on fake sites
- Credential stuffing: Stolen passwords from one breach are replayed across accounts
- Brute force: Automated tools guess weak passwords
- Reuse: Users recycle the same password across multiple systems
- Bulk theft: Attackers steal credential databases in breaches

Credential-based breaches cost an average of $4.81 million and take 292 days to identify and contain— the longest detection-to-containment cycle of any attack type.
The same weaknesses that expose digital systems extend directly into the physical world. In ports, warehouses, and server rooms, passwords and PINs introduce a separate layer of risk that's harder to audit and easier to exploit.
Physical Access Vulnerabilities
In physical access control, credential-based systems create compounding problems:
- Buddy punching: One employee clocks in for another (affecting 19% of employees, costing 2.2% of gross payroll)
- Shared access codes: PINs are written down, texted, or verbally shared
- No accountability: No indisputable record of who entered a space
- Credential transfer: Badges and codes can be lent or stolen without detection
When access credentials can be shared, guessed, or handed off, no audit trail holds up — and that's a direct exposure for compliance, insurance, and workplace safety.
Types of Passwordless Authentication: Setting the Stage
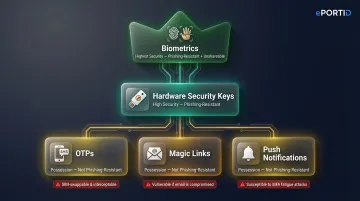
Five main passwordless methods are in use today:
One-Time Passwords (OTPs) sent via SMS or authenticator app Possession-based tier. Vulnerable to SIM swapping — the FBI investigated 1,075 SIM swap attacks in 2023 resulting in $50 million in losses. Not phishing-resistant.
Magic Links delivered via email Possession-based tier. If the email account is compromised, access is compromised. Not phishing-resistant.
Push Notifications requiring approval on a registered device Possession-based tier. Vulnerable to "push bombing" — attackers flood users with approval requests until one is accidentally accepted. Not phishing-resistant.
Hardware Security Keys (USB/NFC tokens) High security tier. FIDO2-certified keys are phishing-resistant. Google eliminated phishing among 85,000+ employees after mandating them. The drawback: keys can be lost or shared, and physical distribution at scale is costly.
Biometric Authentication Highest security tier. Ties identity to physical traits that cannot be transferred or stolen — and unlike a key or token, there is nothing to forget or lose. Combined with liveness detection, biometrics are phishing-resistant and defeat spoofing attempts at the point of scan.
That distinction matters most in high-stakes environments. For critical infrastructure, restricted facilities, or regulated data environments, the authentication method must be impossible to share, delegate, or spoof — and biometrics are the only method on this list that delivers all three by design.
Why Biometrics Is the Strongest Form of Passwordless Authentication
Biometric identifiers—fingerprints, facial geometry, iris patterns, palm veins—are unique to every individual. They cannot be forgotten, lent to a colleague, replicated from a sticky note, or stolen in a phishing email. Not all biometric modalities hold up equally under real-world conditions, though. Understanding where each one falls short explains why certain deployments demand more than a fingerprint reader.
Biometric Modalities and Their Limitations
Fingerprint scanning: Widely used and cost-effective, but fails with cuts, dirt, or calluses—common in industrial settings.
Facial recognition: Convenient but can be spoofed with photos unless liveness detection is implemented. NIST's ongoing Face Analysis Technology Evaluation confirms that presentation attack detection for facial recognition remains variable.
Iris scanning: High accuracy, but requires controlled lighting and close proximity—less practical for high-throughput environments.
Palm vein scanning: Contactless, highly accurate, works even with dirty or damaged hands, and exceptionally difficult to replicate. The vascular pattern lies beneath the skin surface, making surface contamination irrelevant.
Why Palm Vein Biometrics Excel in Demanding Environments
Palm vein biometrics offer structural advantages over surface-based methods:
- Subsurface reading: Vein patterns are beneath the skin and require blood flow to be detected—intrinsic liveness detection
- Environmental resilience: Works with dirty, wet, calloused, or gloved hands
- Exceptional accuracy: Fujitsu PalmSecure reports a false acceptance rate of 0.00001% and false rejection rate of 0.01%
- High data density: Uses 10x the data points of finger vein modalities
- Unique even in identical twins: IEEE research using 234 genetically identical vein pairs confirmed patterns are distinguishable due to stochastic angiogenesis during fetal development
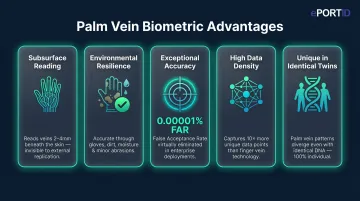
ePortID's contactless palm vein solution—accurate to 99.99991%, verified in under 2 seconds, with built-in liveness detection—has been field-proven with the US Navy, Marine Corps, and commercial clients including Dow Chemical, Fiserv, and South Jersey Port Corp.
That strength raises a fair question: what happens if a biometric template is ever compromised? Unlike a password, you cannot "reset" a fingerprint—so the architecture around biometric data matters as much as the modality itself.
Addressing the "What If Biometrics Are Compromised?" Concern
Modern biometric systems address this risk through:
- Template encryption: Biometric data is converted to encrypted templates, not stored as raw images
- On-device storage: Biometric data never leaves the user's device in FIDO2 implementations
- No central database: Templates are stored locally or on credentials, preventing bulk theft
- Liveness detection: Systems verify the biometric comes from a living person in real time
For enterprise environments handling regulated data or critical access points, this distributed, encrypted model means a breach of one credential vault cannot cascade into an organization-wide identity failure.
The Benefits of Biometric Passwordless Authentication
Biometric passwordless authentication pays off across every part of an organization — from the security perimeter to the payroll ledger. For facilities where identity mistakes carry real consequences, the case for switching is straightforward.
Security
- Eliminates phishing, credential stuffing, and brute force attacks
- Prevents buddy punching and shared credential access
- Creates indisputable audit trails tied to verified individual identity
- Google's deployment of hardware keys resulted in zero confirmed account takeovers since 2017
Operations and Cost
- Reduces password reset tickets (which consume 20–50% of help desk calls at $70 per ticket)
- Eliminates buddy punching (costing 2.2% of gross payroll)
- Simplifies onboarding — no credentials to issue or manage
- Most systems recover their cost within 3–6 months through payroll accuracy alone
User Experience
- Authentication in under 2 seconds
- No memorization, no device to carry, no app to install
- Works for non-technical workforces across shifts and roles
Compliance and Audit Readiness
- Supports HIPAA (45 CFR 164.312), NERC CIP-006-6, and PCI DSS 4.0 MFA requirements
- Meets TWIC verification standards for maritime and port facilities
- Produces tamper-resistant records that hold up under regulatory audit
Industries Where Biometric Passwordless Authentication Is Non-Negotiable
Some environments simply can't rely on passwords, badges, or PINs — the consequences of a breach are too severe. Across these sectors, biometric authentication has moved from "nice to have" to baseline requirement:
- Critical infrastructure — Seaports, oil refineries, power stations, and military bases operate under NERC CIP-006-6, which mandates two or more physical access controls (biometrics included) for high-impact systems. Only verified personnel get through.
- Healthcare and financial services — HIPAA and PCI-DSS compliance demands tight access control without slowing down shift workers. Biometric authentication handles both: fast enough for a busy ER, secure enough for a server room or transaction terminal.
- Warehouses, factories, and enterprise campuses — Large hourly workforces create real exposure to buddy punching and payroll fraud. Biometric time-and-attendance closes that gap. ePortID has deployed this approach for South Jersey Port Corp., Tata Steel, and Thyssen Krupp — environments where accuracy isn't optional.
Frequently Asked Questions
What are the benefits of biometric passwordless authentication?
Biometrics eliminate stolen or shared credentials, require no passwords to remember, verify identity in seconds, create auditable access records, and reduce operational costs. They're ideal for both cybersecurity and physical security applications where accountability is non-negotiable.
What are the main types of biometric passwordless authentication?
Primary modalities include fingerprint scanning, facial recognition, iris scanning, voice recognition, and palm vein scanning. Each differs in accuracy, environmental suitability, and spoofing resistance — with contactless options like palm vein preferred in high-security or hygiene-sensitive environments for their subsurface pattern reading and built-in liveness detection.
Is passwordless authentication more secure than traditional passwords?
Yes. Passwordless authentication removes the attack surfaces passwords create—phishing, brute force, credential stuffing—and replaces them with factors tied to physical possession or biological identity that cannot be guessed or transmitted. CISA identifies phishing-resistant passwordless methods as the gold standard for security.
Can biometric data be stolen or duplicated?
Enterprise-grade biometric systems store encrypted templates (not raw images) on-device or locally, and use liveness detection to reject spoofing attempts — preventing bulk remote theft. Subsurface biometrics like palm vein patterns are especially difficult to duplicate since they cannot be lifted from a surface or photographed.
What is the difference between passwordless authentication and MFA?
MFA adds a second verification step on top of a password. Passwordless authentication removes the password entirely, using only possession and inherence factors. The strongest implementations combine both for "passwordless MFA"—two non-password factors for phishing-resistant authentication.
What industries benefit most from biometric passwordless authentication?
Critical infrastructure (ports, power stations, military), healthcare, financial services, and large industrial operations gain the most. Access control failures in these sectors trigger regulatory penalties, safety incidents, or direct financial loss — not just data exposure. Biometric authentication directly addresses compliance requirements and eliminates shared-credential vulnerabilities.


