
Introduction
Identity-based breaches continue to cripple enterprise security. The average cost of a data breach in the United States reached $10.22 million in 2025, with 88% of basic web application breaches involving stolen credentials. For organizations protecting ports, data centers, power stations, and financial institutions, traditional access controls—passwords, PINs, and ID cards—represent single points of failure that can be lost, shared, or stolen.
Biometric authentication addresses that vulnerability directly — tying access to something a person is, not something they carry or remember. But not all biometric methods are equal. The one you choose determines your exposure to spoofing, compliance gaps, and operational friction. What follows is a breakdown of the top five biometric authentication methods for enterprise security in 2026 — their specific strengths, limitations, and a decision framework to find the right fit for your environment.
TL;DR
- Biometric authentication verifies identity using unique physical or behavioral traits, eliminating credential-based vulnerabilities
- Top methods for 2026: palm vein scanning, fingerprint scanning, facial recognition, iris scanning, and behavioral biometrics
- Data centers, ports, and critical infrastructure require contactless methods with built-in liveness detection
- Evaluate methods against security tier, regulatory requirements, environment, and total cost of ownership
- Most enterprise deployments combine two methods across different access zones rather than relying on one
Why Enterprise Security Demands More Than Passwords in 2026
Biometric authentication uses unique physiological or behavioral identifiers to confirm identity for facility access, system entry, or sensitive data protection. Unlike credentials that can be compromised, biometrics are inherently tied to the individual — they can't be lost, shared, or stolen.
That inherent advantage is driving rapid adoption. The global biometric system market is projected to grow from $53.22 billion in 2025 to $95.14 billion by 2030, a CAGR of 12.3% — driven by organizations that can no longer afford credential-based risk.
NIST Special Publication 800-63B makes the case plainly: passwords are not phishing-resistant, and humans have a limited ability to memorize complex, arbitrary secrets. In 2026, enterprises face a dual security challenge:
- Physical access points — server rooms, loading docks, restricted floors, and facility perimeters
- Digital systems — data networks, application logins, and sensitive record access
Credential-based methods leave both exposed. Biometrics secures both layers with a single, non-transferable factor tied directly to the person standing at the door or the keyboard.
Top 5 Biometric Authentication Methods for Enterprise Security in 2026
These methods are evaluated on accuracy, spoofing resistance, contactless capability, deployment suitability for critical environments, and liveness detection—factors that matter most when access control failures carry operational and safety consequences.
Palm Vein Scanning
Palm vein scanning uses near-infrared light to map the unique pattern of subcutaneous blood vessels in the palm. This biometric is entirely internal, impossible to observe or replicate from a surface, and stable across a person's lifetime.
Why it stands out: The pattern derives from 5 million data points, creating a signature shared by no one else, not even identical twins. Verification is contactless and completes in under two seconds. Liveness detection is built into the scan, meaning a severed hand or artificial replica cannot trigger a false positive.
Fujitsu's PalmSecure F-Pro operates with a False Acceptance Rate (FAR) of under 0.00001% and a False Rejection Rate (FRR) of 1.0%. In 2024, iBeta testing confirmed 0% Attack Presentation Classification Error Rate (APCER) for Level 1 attacks under ISO/IEC 30107-3 standards.
ePortID, in partnership with Fujitsu, delivers this technology to clients including Fiserv, Dow Chemical, South Jersey Port Corp., and Tata Steel, with accuracy reaching 99.99991%.
| Feature | Specification |
|---|---|
| Accuracy & Speed | Near-zero false acceptance rate; verification in under 2 seconds |
| Spoofing Resistance | Extremely high—internal vascular pattern cannot be duplicated; liveness detection built in |
| Ideal Enterprise Deployment | Data centers, port facilities, military bases, refineries, server rooms, financial institutions |
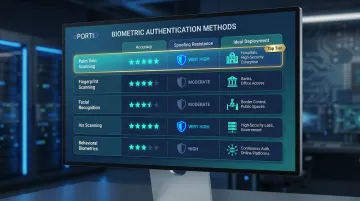
Fingerprint Scanning
Fingerprint scanning remains the most widely deployed biometric modality globally, analyzing the unique ridge-and-valley patterns on a fingertip via optical, capacitive, or ultrasonic sensors.
Trade-offs: Cost-effective and easy to integrate with existing systems, but contact-based (raising hygiene concerns in industrial and healthcare environments). The LivDet 2023 competition revealed that Attack Presentation Classification Error Rate (APCER) spiked to 39.58% when systems faced unknown presentation attacks. Performance degrades with worn, wet, or damaged skin—a practical issue in port, warehouse, and manufacturing settings.
| Feature | Specification |
|---|---|
| Accuracy & Speed | High accuracy under standard conditions; speed varies by sensor type (1-3 seconds) |
| Spoofing Resistance | Moderate—latent print replication is a documented attack vector; liveness detection varies by vendor |
| Ideal Enterprise Deployment | Office environments, IT access control, time and attendance in low-to-medium risk settings |
Facial Recognition
Facial recognition maps the geometric relationships between facial features using 2D or 3D cameras and AI-powered matching algorithms, enabling hands-free, high-throughput identity verification.
NIST's Face Recognition Technology Evaluation (FRTE) 1:N benchmark shows top-tier algorithms can achieve a False Negative Identification Rate (FNIR) of just 0.0017 at a False Positive Identification Rate (FPIR) of 0.001 across a gallery of 12 million subjects.
That said, Gartner predicts that by 2026, 30% of enterprises will consider facial biometric authentication unreliable in isolation due to a 200% increase in AI-generated deepfake injection attacks. 3D depth sensing and liveness detection are now critical requirements.
| Feature | Specification |
|---|---|
| Accuracy & Speed | High with 3D sensing; frictionless and near-instant at entry points |
| Spoofing Resistance | Moderate to high depending on depth-sensing and liveness detection capability; deepfake risk is a growing concern |
| Ideal Enterprise Deployment | Building entry, airport security, workforce management, healthcare patient ID |
Iris Scanning
Iris scanning uses infrared imaging to map the unique textural patterns in the colored ring of the eye, a biometric feature that is stable from infancy, highly distinctive, and protected internally by the cornea.
Iris scanning offers some of the highest accuracy rates among all biometric modalities and requires no physical contact. NIST Special Publication 800-76-2 establishes a maximum allowed False Match Rate (FMR) of 0.0001 for off-card iris image matching in federal personal identity verification systems.
In practice, the technology demands more controlled lighting and deliberate positioning from the user. Eyeglasses, eyelash occlusion, off-angle capture, and medical conditions like cataracts can drive up segmentation errors. Hardware costs range from $1,500 to $3,000 per unit, higher than fingerprint or facial systems.
| Feature | Specification |
|---|---|
| Accuracy & Speed | Very high accuracy; 1-3 seconds; sensitive to ambient light and user positioning |
| Spoofing Resistance | Very high—iris texture is internal and difficult to replicate; liveness detection available |
| Ideal Enterprise Deployment | Government facilities, research labs, high-security data centers, border control |

Behavioral Biometrics
Behavioral biometrics authenticates users based on patterns in how they interact with systems: keystroke dynamics, mouse movement, typing rhythm, and gait. The result is a continuous authentication layer that operates invisibly in the background.
The behavioral biometrics market is expected to reach $10.5 billion by 2033, driven by adoption in banking and financial services. BioCatch processes over 15 billion user sessions monthly, with one UK bank detecting 81% of fraudulent transactions while keeping the false positive rate below 0.05%.
One important boundary: NIST SP 800-63B explicitly states behavioral biometrics do not establish "authentication intent" and cannot serve as standalone physical access credentials. They are most effective as a continuous session-level layer within digital environments, complementing physical biometric methods in zero-trust architectures.
| Feature | Specification |
|---|---|
| Accuracy & Speed | Moderate standalone; highly effective as a continuous layer within authenticated sessions |
| Spoofing Resistance | High for continuous use—patterns are difficult to consciously replicate over extended sessions |
| Ideal Enterprise Deployment | Digital access monitoring, financial transaction systems, remote workforce security, zero-trust layering |
How to Choose the Right Biometric Authentication Method for Your Enterprise
Security Tier and Environment Type
The physical environment and consequence of unauthorized access should drive method selection. A server room or chemical plant carries a fundamentally different risk profile than a general office. High-security environments require methods with near-zero false acceptance rates, built-in liveness detection, and resistance to insider spoofing attempts.
Contactless vs. Contact Requirements
Industrial settings introduce practical barriers for contact-based methods. Contactless methods (palm vein, iris, facial) eliminate these failure modes entirely. Common contact-based degraders include:
- Gloves or protective hand coverings
- Wet or oily hands from work conditions
- Skin abrasions or calluses affecting fingerprint reads
- Hygiene protocols requiring glove use between scans
Regulatory and Compliance Alignment
Enterprises in specific sectors face mandated identity assurance requirements:
| Regulation/Standard | Biometric Requirement |
|---|---|
| TWIC (TSA/DHS) | TWIC card readers must perform biometric fingerprint match to confirm the person presenting the card is the rightful holder |
| CMMC Level 2/3 (DoD) | Requires Multifactor Authentication (MFA) for network access; biometrics ("something you are") are explicitly approved |
| HIPAA Security Rule | 45 CFR 164.312(d) requires "Person or entity authentication"; biometrics (fingerprints, facial, iris, palm vein) are valid technical safeguards |
| NERC CIP-006 | Requires two or more different physical access controls for High Impact BES Cyber Systems; two-factor authentication combining card key and biometric satisfies this requirement |
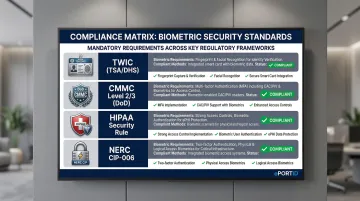
Confirm whether your chosen biometric method's accuracy and auditability satisfy these requirements. ### Total Cost of Ownership and ROI
Upfront hardware costs vary significantly: fingerprint scanners range from $50 to $1,500, iris scanners from $1,500 to $3,000, and palm vein systems typically fall between $2,000 and $5,000. These figures, however, only tell part of the story.
Evaluate hardware costs against measurable operational savings. "Buddy punching" costs U.S. employers approximately $373 million annually, averaging 2.2% of gross payroll. Nucleus Research found that automating time and attendance with biometric systems can deliver ROI in fewer than 9 months — through time theft elimination, reduced payroll processing overhead, and prevention of unauthorized access incidents.
Integration with Existing Identity and Access Management (IAM) Infrastructure
The biometric method must integrate cleanly with your existing access control systems, HR platforms, and audit logging requirements. Contactless solutions with API-accessible enrollment workflows reduce friction during enterprise-wide rollout. Verify compatibility across:
- Physical access control: Wiegand and OSDP protocol support
- Logical access: Active Directory, Okta, or equivalent IAM platform integration
- HR and payroll systems: Enrollment sync and attendance data export
How We Evaluated These Methods
Each method was assessed against five criteria grounded in real-world enterprise deployment requirements:
- Documented accuracy — False Acceptance Rate (FAR) and False Rejection Rate (FRR)
- Liveness detection — availability and robustness of Presentation Attack Detection (PAD)
- Infrastructure suitability — performance in physical, industrial, and high-security environments
- Enterprise scalability — viability for large-scale, multi-site deployment
- Adoption evidence — documented use in high-security sectors such as defense, finance, and critical infrastructure
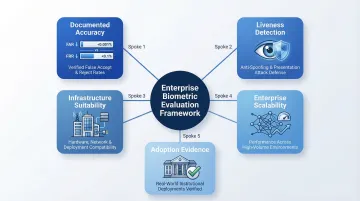
These criteria were then cross-referenced against published benchmarks from three authoritative testing frameworks.
Authoritative Evaluation Frameworks:
- NIST FRTE & FATE: Measures 1:1 and 1:N algorithmic accuracy (FNMR, FNIR, FPIR) and Presentation Attack Detection (PAD) capabilities
- NIST IREX: Evaluates automated iris recognition algorithms for 1:N identification accuracy
- ISO/IEC 30107-3: Establishes testing methodology for Presentation Attack Detection, defining Attack Presentation Classification Error Rate (APCER) and Bona Fide Presentation Classification Error Rate (BPCER)
Methods were deprioritized when they present a single point of failure specific to 2026 threat conditions. Disqualifying factors include spoofability via deepfake, contact requirements in hygiene-sensitive environments, and environmental sensitivity that prevents reliable deployment in industrial settings.
Conclusion
No single biometric method is universally superior. For enterprises protecting critical physical and digital assets in 2026, the evaluation must prioritize accuracy, liveness detection, contactless operation, and compliance alignment over adoption convenience or cost alone.
Decision-makers should assess not just initial deployment cost but long-term scalability, resistance to evolving spoofing technologies, and the operational ROI that comes from eliminating credential-based vulnerabilities. A system that scores well across all four criteria — accuracy, liveness, contactless operation, and compliance — will outlast vendor lock-in, regulatory changes, and the next generation of spoofing attacks.
For organizations securing ports, data centers, financial facilities, or critical infrastructure, ePortID's contactless palm vein scanning solution delivers 99.99991% accuracy with sub-2-second verification and built-in liveness detection. Built on 20 years of experience serving the US Navy, Army JTF, and port authorities, and powered by Fujitsu technology, ePortID has a proven deployment record with clients including Fiserv, Dow Chemical, and Tata Steel. Contact ePortID at 215-627-2651 or info@eportid.com to discuss your access control requirements.
Frequently Asked Questions
What is the most accurate biometric authentication method for enterprise security?
Palm vein scanning and iris recognition currently offer the highest documented accuracy rates (lowest false acceptance rates). Palm vein scanning is particularly notable for its liveness detection capability and resistance to spoofing, making it well-suited for critical infrastructure environments where unauthorized access carries significant operational and safety consequences.
How does palm vein scanning differ from fingerprint scanning?
Palm vein scanning reads an internal vascular pattern using infrared light, making it contactless, hygienic, and impossible to spoof from a surface trace. Fingerprint scanning reads an external surface pattern that can be replicated, degraded by skin conditions, and requires physical contact with the sensor.
Can biometric authentication systems be fooled or spoofed?
Spoof resistance varies by method. Contact fingerprint and 2D facial systems are more vulnerable to presentation attacks, with documented success rates exceeding 30% against unknown spoof materials. Internal biometrics like palm vein and iris—both with built-in liveness detection—offer the strongest protection against physical spoofing and AI-generated attack vectors.
What biometric method works best for industrial or outdoor enterprise environments?
Contactless methods—particularly palm vein scanning and iris recognition—perform most reliably in industrial settings where glove use, physical labor, ambient lighting variation, and hygiene protocols make contact-based or camera-sensitive systems prone to failure. Palm vein systems operate across temperature ranges from -25°C to +80°C (-13°F to +176°F), ensuring reliable deployment in diverse conditions.
Are biometric authentication systems compliant with enterprise data privacy regulations?
Compliance depends on how biometric templates are stored and processed. On-device or encrypted storage models align with GDPR, CCPA, BIPA, and HIPAA requirements. Verify that your vendor's architecture supports your specific obligations around template encryption, storage location, and data retention.
How long does it take for an enterprise biometric system to deliver ROI?
Most enterprises deploying biometric access control and time/attendance systems recoup implementation costs within 3 to 6 months. Returns come through eliminating buddy punching (which costs organizations 2.2% of gross payroll annually), reducing payroll errors, and lower credential management costs.


