What is an access control integrator?
An access control integrator is a specialized security professional who designs, configures, and implements comprehensive access control systems by connecting various hardware and software components into a unified security ecosystem. They ensure biometric readers, controllers, locks, and monitoring software work seamlessly with your existing infrastructure—whether integrating with legacy badge systems via Wiegand protocol, connecting to network management platforms, or coordinating multi-site deployments. The integrator handles technical specifications, protocol compatibility, real-time alert configuration, and audit trail setup to deliver a turnkey solution tailored to your facility's specific security requirements and operational workflows.
What is the role of a systems integrator?
A systems integrator serves as the architect and project manager for complex security deployments, translating business security requirements into functional technical solutions. They assess your current infrastructure, identify integration points and potential vulnerabilities, specify appropriate hardware and software components, configure communication protocols between disparate systems, and ensure all elements work together reliably. Beyond initial installation, they establish monitoring capabilities, configure user permissions and access hierarchies, set up reporting and compliance features, and provide training to ensure your team can manage the system effectively. Their expertise prevents costly compatibility issues and ensures your investment delivers measurable security improvements from day one.
How does palm vein biometric technology differ from fingerprint scanning?
Palm vein biometrics reads the unique pattern of blood vessels beneath the skin surface using near-infrared light, making it completely contactless and impossible to replicate or steal. Unlike fingerprint scanners that can be fooled by lifted prints or degraded by worn skin, palm vein patterns are internal to the body, check for liveness during each scan, and remain stable throughout a person's lifetime. The technology achieves 99.99991% accuracy using 5 million data points—so precise that even identical twins have different patterns. Verification completes in under 2 seconds without requiring users to touch any surface, improving hygiene while eliminating common biometric vulnerabilities.
Can your access control systems integrate with our existing security infrastructure?
Yes, our solutions are designed for seamless integration with virtually all existing access control platforms through industry-standard Wiegand and OSDP protocols. We can interface with your current electric strikes, mag-locks, turnstiles, vehicle gates, and access control panels without requiring a complete system replacement. For data access management, our scanner mouse technology works standalone on any Windows PC, tablet, or laptop, or can connect multiple locations via secure VPN using locked static IPs. We assess your current infrastructure during the consultation phase and design an integration approach that preserves your existing investment while adding biometric security capabilities and real-time monitoring features.
What kind of audit trail and reporting capabilities do your systems provide?
Our access control systems create comprehensive, immutable audit trails capturing every entry and exit attempt with timestamp, location, user identity, authentication method used, and access decision (granted or denied). The platform tracks duration of stay, identifies unusual patterns like after-hours access or multiple rapid entry attempts, and sends real-time alerts for security events such as denied access by terminated employees or tailgating detection. All data synchronizes to centralized dashboards for multi-location visibility, with customizable reports for compliance documentation, trend analysis, and operational insights. Audit records are timestamped and archived to meet regulatory requirements for industries like healthcare, finance, and critical infrastructure.
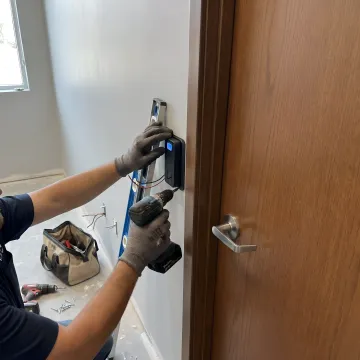
How long does a typical access control system integration take?
Implementation timelines vary based on facility size and complexity, but most single-door or small office deployments complete within 2-3 business days, while enterprise installations with multiple entry points and locations typically require 1-3 weeks. The process includes site survey and requirements analysis, hardware specification and ordering, physical installation of readers and controllers, network configuration and protocol integration, user enrollment and training, and system testing with live operations. Our 20 years of integration experience allows us to minimize operational disruption through phased rollouts and after-hours installation when needed. We provide detailed project timelines during the assessment phase so you can plan accordingly.
What ongoing maintenance and support do your systems require?
Our contactless palm vein readers require minimal maintenance due to their solid-state design with no moving parts or surfaces that degrade over time. Basic upkeep involves occasional cleaning of the scanner window and standard network system monitoring. We include a two-year manufacturer warranty covering defects and provide ongoing technical support for system administration, user enrollment, and troubleshooting. Software updates deploy remotely to add features and maintain security compliance. For enterprise deployments, we offer service agreements that include priority support, preventive maintenance visits, and guaranteed response times to ensure your security infrastructure maintains optimal performance with minimal internal IT burden.
How do you handle enrollment for large organizations with hundreds of employees?
Our enrollment process is designed for speed and scalability—each user enrollment takes approximately 30 seconds and follows a simple workflow where employees scan their palm three times to capture their unique vein pattern. For large organizations, we deploy mobile enrollment stations that can be set up in common areas, allowing employees to self-enroll with minimal supervision during shift changes or scheduled sessions. The system's "enroll once and done" capability means each user's biometric template works across all connected access points and systems—door entry, time clocks, data access, and any other integrated applications—eliminating redundant enrollment processes and accelerating deployment across your entire organization.