
Introduction
Attacks on energy grids, seaports, military bases, and financial systems have accelerated dramatically, transforming security investment from a compliance checkbox into a survival imperative. CISA blocked 371 million malicious connections within critical infrastructure in 2025 alone, while the average eCrime breakout time plummeted to just 29 minutes—with the fastest recorded at 27 seconds.
Critical infrastructure facilities require layered protection across both physical access and cyber domains simultaneously. Generic IT security approaches consistently fall short because they address only digital threats while leaving physical entry points vulnerable to credential sharing, badge theft, and insider threats.
That gap is exactly what threat actors exploit. This article ranks the best security solutions for critical infrastructure in 2026, evaluated across physical, cyber, and identity security dimensions.
TLDR
- Critical infrastructure faces simultaneous cyber and physical threats requiring solutions that address both attack surfaces
- Top solutions combine AI-driven threat detection, Zero Trust network access, and physical identity verification
- Contactless palm vein scanning eliminates credential vulnerabilities that plague badge and PIN systems
- ePortID, Palo Alto Networks, Claroty, Genetec, and CrowdStrike each cover a distinct security layer — together they close the gaps no single tool can
- Choose solutions based on sector fit, integration capability, compliance requirements, and coverage across both cyber and physical threats
Overview of Security Solutions for Critical Infrastructure
Critical infrastructure security solutions in 2026 cover tools, platforms, and systems that protect facilities, networks, operational technology (OT), and identities across energy, ports, defense, healthcare, and financial services. CISA defines 16 such sectors as so vital that their incapacitation would have debilitating effects on national security, economic stability, or public health.
The scale of the threat is concrete. According to CISA's 2025 Year in Review, the agency blocked 2.62 billion malicious connections on federal civilian networks and 371 million within critical infrastructure. Meanwhile, 50% of all global ransomware attacks in 2025—2,332 incidents—targeted critical infrastructure sectors, a 34% year-over-year increase.
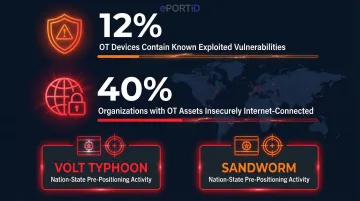
Legacy unpatched systems remain the primary entry points. Claroty's 2025 research on nearly one million OT devices found:
- 12% contain Known Exploited Vulnerabilities (KEVs)
- 40% of organizations have these assets insecurely connected to the internet
- Nation-state actors like Volt Typhoon and Sandworm actively exploit internet-facing OT devices to pre-position for disruptive attacks
The five solutions below were selected for proven effectiveness and sector relevance. Each addresses the dual challenge of physical and cyber security—because in critical infrastructure, a gap in either creates a gap in both.
Best Security Solutions for Critical Infrastructure in 2026
These solutions were evaluated on reliability, depth of protection (physical + cyber), sector-specific deployment track record, technology innovation, and client trust across government, energy, defense, and industrial verticals.
ePortID
ePortID is a Philadelphia-based contactless biometric identity verification provider with 20 years of experience securing military installations—including US Navy, Army JTF, and Marine Corps facilities—and commercial port authorities. Commercial clients include Fiserv, Dow Chemical, South Jersey Port Corp., Tata Steel, and Thyssen Krupp.
ePortID stands out through its Fujitsu-partnered palm vein scanning technology that derives identity from 5 million unique data points, accurate to 99.99991% in under 2 seconds. The system checks for liveness during every scan and produces credentials that cannot be lost, shared, forgotten, duplicated, or stolen—eliminating the vulnerabilities inherent in badge or PIN-based systems. Unlike legacy access control, palm vein patterns exist only beneath the skin and cannot be forged or replicated.

The technology addresses a costly security gap: buddy punching (time theft through shared credentials) costs US employers approximately $11 billion annually, averaging $1,560 per employee over the course of a year. By making credential sharing physically impossible, ePortID delivers measurable ROI within 3–6 months through payroll savings and operational efficiency gains.
| Category | Details |
|---|---|
| Key Features | Contactless palm vein biometric; liveness detection; under-2-second verification; 99.99991% accuracy; eliminates buddy punching and unauthorized access |
| Best For | Seaports, airports, military bases, power stations, refineries, data centers, oil rigs, financial institutions, hospitals |
| Notable Differentiator | Military-grade deployment history; Fujitsu partnership; pays for itself in 3–6 months through payroll and operational savings |
Palo Alto Networks
Palo Alto Networks is a global leader in AI-driven network security, offering next-generation firewalls, the Prisma Cloud platform, and Cortex XDR. The company was named a Leader in the 2025 Gartner Magic Quadrant for Security Service Edge for the third consecutive year and in the inaugural 2025 Gartner Magic Quadrant for Hybrid Mesh Firewalls.
For critical infrastructure, Palo Alto Networks stands out through AI and machine learning algorithms that detect novel and sophisticated threats in real time, reducing false positives. This capability is particularly valuable for understaffed facilities that need reliable cyber defenses without scaling headcount. The platform's alignment with NIST Cybersecurity Framework and IEC 62443 standards ensures compliance with regulatory requirements governing critical infrastructure protection.
A $65 million Enterprise License Agreement with the Department of Energy's National Nuclear Security Administration and documented incident response for defense contractors breached by Advanced Persistent Threats speaks to its depth of real-world deployment.
| Category | Details |
|---|---|
| Key Features | Next-gen firewalls; Cortex XDR for endpoint and network detection; Prisma Cloud for cloud workload protection; AI-driven threat intelligence |
| Best For | Energy grids, government networks, financial institutions, defense supply chains |
| Notable Differentiator | Consistently top-rated in independent security evaluations; strong compliance alignment with NIST and CISA frameworks |
Claroty
Claroty is a specialized OT/ICS/IoT security platform purpose-built for operational technology environments—the control systems that run power plants, water treatment facilities, oil refineries, and manufacturing lines that traditional IT security tools fail to protect adequately. The company was named a Leader in the 2025 Gartner Magic Quadrant for CPS Protection Platforms, positioned highest for Ability to Execute and furthest for Completeness of Vision.
Claroty provides deep visibility into OT/ICS network assets, including legacy devices that cannot be patched. The platform offers continuous monitoring and anomaly detection that respects the availability constraints of critical operational systems—preventing disruptions even during active threat response. This capability matters because OT downtime carries staggering costs: $2.3 million per hour in automotive manufacturing, $500,000+ per hour in oil and gas.
Documented deployments include:
- A national electric generation company deploying Continuous Threat Detection across nationwide power plants for full asset visibility
- A major US water utility serving 2 million+ residents achieving compliance with America's Water Infrastructure Act across 20+ dispersed facilities
| Category | Details |
|---|---|
| Key Features | OT/ICS/IoT asset discovery; continuous threat monitoring; vulnerability management for legacy devices; network segmentation enforcement |
| Best For | Power generation, oil and gas, water utilities, manufacturing, and other OT-heavy critical infrastructure sectors |
| Notable Differentiator | One of the few solutions designed specifically for environments where downtime is not acceptable and many endpoints cannot receive security patches |

Genetec
Genetec is a unified physical security platform combining video surveillance, access control, and license plate recognition into a single, centrally managed system. Serving over 42,500 customers via an extensive network of channel partners in over 159 countries, airports, seaports, transit authorities, and government facilities deploy Genetec to manage physical security at scale.
Genetec's open-architecture approach integrates with thousands of third-party hardware and software systems—including biometric devices—through partnerships with over 180 technology providers. The platform provides cyber-hardened video and access control infrastructure and enables security teams to correlate physical and cyber events in a single pane of glass.
The company maintains stringent certifications including ISO/IEC 27001, ISO/IEC 27017, SOC 2 Type II, and UL 2900-2-3 Level 3 cybersecurity readiness. Notable deployments include London Heathrow Airport's 9,000-camera system monitoring 150km of baggage belts and 150,000 daily vehicles, and the Port of Moerdijk's unified system coordinating incident response across an industrial zone housing 400 companies.
| Category | Details |
|---|---|
| Key Features | Unified access control and video surveillance; open platform integration; cyber-resilient architecture; real-time incident correlation |
| Best For | Airports, seaports, transit systems, government campuses, large industrial facilities |
| Notable Differentiator | Trusted by thousands of critical infrastructure operators globally; strong alignment with physical security compliance requirements |
CrowdStrike
CrowdStrike is the leading cloud-native endpoint security and threat hunting platform, with its Falcon platform deployed across critical infrastructure operators globally to detect, investigate, and neutralize cyber threats at the device and network level before they escalate to operational disruption. The company was named a Leader for the sixth consecutive time in the 2025 Gartner Magic Quadrant for Endpoint Protection Platforms.
In the 2025 MITRE ATT&CK Enterprise Evaluations—featuring cross-domain attacks emulating SCATTERED SPIDER and MUSTANG PANDA threat actors—CrowdStrike delivered:
- 100% detection rate
- 100% protection rate
- Zero false positives
The platform's AI-powered Threat Graph and cloud-native architecture enable real-time detection across millions of endpoints simultaneously.

The dedicated Overwatch managed threat hunting team provides active human-in-the-loop defense—particularly valuable for critical infrastructure sectors targeted by nation-state actors. CrowdStrike's 2026 Global Threat Report observed an 89% increase in attacks by AI-enabled adversaries, with 82% of detections being malware-free, highlighting the importance of advanced behavioral detection capabilities.
| Category | Details |
|---|---|
| Key Features | Cloud-native endpoint protection; Falcon platform with AI/ML threat detection; Overwatch managed threat hunting; rapid deployment with minimal infrastructure |
| Best For | Data centers, financial institutions, healthcare networks, defense contractors, energy sector OT-adjacent IT environments |
| Notable Differentiator | Proven track record against nation-state adversaries; fast deployment without on-premises hardware; scalable from SMB to federal government |
How We Chose the Best Security Solutions
These solutions were assessed across five criteria:
- Proven deployment history: Documented case studies and measurable outcomes in critical infrastructure environments
- Physical and cyber attack coverage: Ability to address the vectors most relevant to the sector, including attacks that exploit the gap between these domains
- Integration capability: Solutions that work together rather than creating security silos
- Regulatory alignment: Compatibility with CISA guidelines, NIST Cybersecurity Framework, IEC 62443, HIPAA, and NIS2
- Total value delivered: ROI from prevented breaches, operational efficiency, and regulatory compliance — not just upfront price
A common mistake operators make is choosing a single-category solution — firewall-only or badge-access-only — and assuming it provides sufficient protection. Critical infrastructure attacks increasingly exploit the gap between physical and cyber security.
For example, an adversary might use stolen credentials to gain physical access to a facility. From there, they connect a rogue device to an internal network and bypass perimeter cyber defenses entirely.
No single solution on this list is intended to stand alone. The strongest security posture for critical infrastructure in 2026 combines physical identity verification, network threat detection, OT monitoring, and unified security management into a layered defense strategy.

Conclusion
The best security solution for critical infrastructure in 2026 is a deliberate, layered strategy that addresses physical access, network security, OT/ICS visibility, and identity verification simultaneously. The solutions covered here represent distinct but complementary categories, each closing gaps that adversaries actively exploit.
Evaluate solutions not just on feature lists but on three practical criteria:
- Sector-specific deployment history — vendors with documented results in your environment, not just comparable ones
- Integration flexibility — how cleanly the solution connects to your existing OT, IT, and physical access layers
- Long-term scalability — whether it can grow with connected devices, remote access points, and evolving compliance requirements
As device counts rise and workforces become more distributed, correlating physical and cyber security events in a single view shifts from a nice-to-have to a hard operational requirement.
For organizations that need to lock down physical access at ports, power stations, military facilities, data centers, or any high-security site, ePortID's contactless palm vein biometric system brings identity verification honed across 20 years of work with the US Navy, Army JTF, Marine Corps, and Port Authorities — and deployed commercially at sites including Dow Chemical, South Jersey Port Corp., and Tata Steel. The system pays for itself in 3 to 6 months. Contact ePortID at info@eportid.com or 215-627-2651 to discuss deployment in your security stack.
Frequently Asked Questions
What is critical infrastructure security and why does it require specialized solutions?
Critical infrastructure security protects systems essential to national function including energy, water, transport, defense, and finance. These environments require specialized solutions because they involve operational technology, legacy systems, and physical facilities that standard IT security tools are not designed to protect—where downtime can have life-threatening consequences and regulatory compliance requirements are uniquely stringent.
What are the biggest cybersecurity threats to critical infrastructure in 2026?
The primary threats include nation-state attacks targeting OT/ICS systems (like Volt Typhoon and Sandworm), ransomware against unpatched legacy infrastructure (50% of 2025 ransomware targeted critical sectors), and exploitation of end-of-life devices. Claroty found that 12% of OT devices contain Known Exploited Vulnerabilities, and 40% of organizations have these assets insecurely connected to the internet.
Why is biometric access control important for critical infrastructure physical security?
Biometrics eliminate the vulnerabilities of shared, stolen, or forgotten credentials that plague badge and PIN systems. Contactless palm vein scanning provides 99.99991% accuracy with liveness detection, so biometric credentials cannot be transferred, duplicated, or stolen. This also eliminates buddy punching, which costs employers $1,560 per employee annually.
What is the difference between OT security and IT security in critical infrastructure?
IT security focuses on data confidentiality and system integrity, while OT security prioritizes availability and physical safety of operational systems like SCADA and ICS. Downtime can cost $2.3 million per hour and carry life-threatening consequences, yet OT systems often run on legacy devices that cannot be patched. This demands specialized monitoring and segmentation that traditional IT tools cannot provide.
What regulatory frameworks govern critical infrastructure security in the US?
Key frameworks include CISA's Binding Operational Directives (BOD 26-02 requires federal agencies to decommission unsupported hardware by 2028) and the NIST Cybersecurity Framework 2.0. Sector-specific standards add further requirements: NERC CIP for energy, IEC 62443 for industrial control systems, and HIPAA for healthcare facilities protecting electronic health information.
How do physical and cyber security solutions work together for critical infrastructure?
Modern security programs integrate physical access control (biometrics, surveillance) with cyber tools (firewalls, SIEM, endpoint protection) so that events in one domain trigger responses in another. A biometric access violation, for instance, can automatically correlate with network monitoring alerts to detect coordinated insider-outsider attacks. This unified approach closes the gaps adversaries exploit between physical and digital domains.


