Introduction
Badges get lost. PINs get shared. Passwords get stolen. But your biology cannot be misplaced.
Critical infrastructure operators—ports, power stations, data centers, and factories—face a security reality where traditional credentials create vulnerabilities, not protection. Time theft and buddy punching cost U.S. employers between 1.5% and 5% of gross payroll annually, while credential theft incidents average $4.8 million per breach. Biometric identity verification addresses these vulnerabilities directly—replacing credentials that can be lost, shared, or stolen with traits that belong exclusively to one person.
That said, biometric technologies vary widely in how they perform under real operational conditions. Choosing the wrong modality can mean the difference between near-perfect security and a system that gets bypassed, rejected, or creates workflow bottlenecks. This guide compares the most widely used biometric technologies across five key metrics: accuracy, spoofability, contactless capability, deployment cost, and use case fit.
TLDR
- Biometric identity verification confirms identity using unique physical traits—more secure than passwords, PINs, or cards
- The five most common technologies (fingerprint, facial, iris, voice, palm vein) each carry distinct accuracy, hygiene, and deployment trade-offs
- For high-security physical access control, accuracy and spoof resistance are paramount—where palm vein scanning consistently leads
- Contactless biometrics matter in environments with hygiene requirements, heavy gloves, or high throughput needs
- Choosing the right technology means matching it to your environment, threat profile, and operational workflow — cost is only part of the equation
Quick Comparison: Biometric Technologies at a Glance
| Technology | Accuracy Level | Contactless | Spoof Resistance | Environmental Sensitivity | Deployment Cost | Best Use Case |
|---|---|---|---|---|---|---|
| Fingerprint Scanning | Moderate (affected by skin wear) | No | Low (prints can be lifted/replicated) | High (fails with wet, dirty, gloved hands) | Low | Consumer devices, low-security office access |
| Facial Recognition | Moderate to High (varies with liveness detection) | Yes | Moderate (vulnerable to photos, deepfakes) | High (degrades with lighting, masks, aging) | Medium | High-throughput public spaces, airports |
| Iris Recognition | Very High | Yes (close range) | Very High | Moderate (requires user positioning) | High | Government, military, border control |
| Voice Recognition | Low to Moderate | Yes (remote) | Low (AI voice spoofing) | Very High (noise, illness affect accuracy) | Low | Phone banking, call centers |
| Palm Vein Scanning | Very High (99.99991%) | Yes | Very High (internal biometric, liveness verified) | Low (unaffected by skin condition) | Medium to High | Critical infrastructure, industrial facilities, data centers |
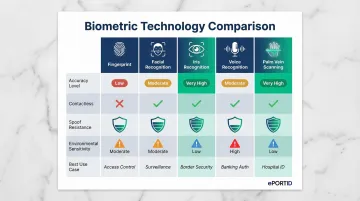
Note: Accuracy figures sourced from NIST biometric evaluation benchmarks, Fujitsu technical documentation, and published independent test results. The sections below explain what drives each rating — and what those ratings mean for facilities where a failed authentication isn't just inconvenient, it's a security breach.
Breaking Down the Major Biometric Technologies
Fingerprint Scanning
Fingerprint scanning captures ridge patterns via optical or capacitive sensors, comparing them against stored templates. It became the most widely deployed biometric due to lower costs, user familiarity, and integration into mobile devices. Organizations default to it for workforce time-and-attendance and building access—it's familiar, inexpensive, and easy to deploy.
Key limitations for industrial or high-security buyers:
- Dirty, wet, or gloved fingers — common in factories, ports, and labs — cause frequent false rejections
- Manual laborers see higher false rejection rates as ridge detail wears down over time
- Latent prints lifted from surfaces can be replicated with moderate effort, creating real vulnerabilities in adversarial environments
Facial Recognition
Facial recognition uses AI algorithms to map facial geometry from camera images and match them against stored templates. Its primary advantage is high-throughput capability for environments like airports and office buildings, requiring no physical contact or deliberate user action. Users simply walk past cameras, enabling frictionless authentication.
Critical limitations:
- Performance degrades with masks, poor lighting, aging, and off-angle camera positioning
- Deepfake and photo spoofing remain active threats unless liveness detection is layered in, which adds both complexity and cost
- Passive facial capture raises regulatory and ethical questions across multiple jurisdictions
For deployments where throughput and convenience matter more than maximum security assurance, facial recognition remains a strong option.
Iris Recognition
Iris recognition stands as one of the highest-accuracy modalities due to the extreme uniqueness and stability of iris patterns. The UAE's Iris Expellee Tracking System processes 2.7 billion cross-comparisons daily with zero recorded false matches, successfully intercepting over 325,000 unauthorized entry attempts. This performance drives strong adoption in government, military, and border control settings where security outweighs user convenience.
Practical trade-offs:
- Requires dedicated infrared scanning equipment, which increases upfront costs significantly
- Users must deliberately position in front of a reader, which slows throughput in high-volume environments
- Daily use at scale — particularly in industrial settings with large workforces — creates meaningful friction
Voice Recognition
Voice biometrics analyze speech patterns — tone, cadence, frequencyBackground noise, illness, or emotional stress all trigger false rejections
- More vulnerable to AI-generated voice spoofing than any other biometric modality — synthetic voice tools now replicate speech patterns with high fidelity
- Not suitable for securing doors, gates, or restricted physical areas
Voice recognition works in narrow remote-authentication contexts. For physical access control, the reliability gap is too wide.
Palm Vein Scanning
Palm vein scanning uses near-infrared light to capture the unique vascular pattern beneath the skin's surface, formed from millions of reference points that remain stable across a person's lifetime. Unlike surface biometrics, this internal pattern cannot be replicated from a surface impression, photo, or external scan.
Core advantages:
- Inherently contactless: no physical touch required, addressing hygiene and PPE concerns
- Vein patterns are internal and only readable in living tissue with active blood flow
- Built-in liveness detection verifies living tissue during the scan itself, with no separate layer needed
- Published benchmarks show 99.99991% accuracy with verification completed in under 2 seconds
Financial institutions like the Reserve Bank of India deployed palm vein technology specifically for its built-in liveness detection and fast processing for both staff and visitors.
Healthcare facilities have enrolled over 5 million patients using palm vein systems, with documented reductions in insurance fraud and administrative overhead.
Key Criteria for Evaluating Biometric Technology for Your Environment
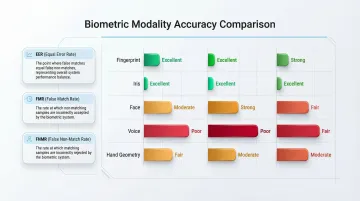
Accuracy and False Rejection Rate (FRR)
In high-security environments, a false acceptance (letting the wrong person in) is a critical failure. But a high false rejection rate creates operational disruption—legitimate users denied access, productivity loss, and user frustration that erodes adoption.
Organizations in critical infrastructure need both metrics extremely low:
- Equal Error Rate (EER): The point where false acceptance and false rejection rates intersect
- False Match Rate (FMR): Probability the system incorrectly matches two different individuals
- False Non-Match Rate (FNMR): Probability the system fails to match the same individual
Palm vein and iris recognition deliver the lowest EER, while fingerprint and facial recognition show higher variability depending on environmental conditions — particularly lighting, skin moisture, and surface contamination.
Spoof and Liveness Resistance
Spoof resistance is non-negotiable in environments where adversarial access attempts are realistic—military bases, refineries, data centers, financial institutions. Each modality handles presentation attacks differently:
- Printed photos: Defeat basic facial recognition without liveness detection
- Silicone fingers: Can fool optical fingerprint scanners
- Recorded voices: Bypass voice authentication systems
- Masks and deepfakes: Compromise facial recognition systems lacking active liveness checks
Palm vein scanning offers inherent spoof resistance because the biometric is internal and requires active blood flow. The system cannot be fooled by photographs, molds, or recordings—only living tissue registers a valid scan.
That internal, liveness-dependent verification also shapes the next decision point for many facilities: whether the system requires physical contact at all.
Contactless Capability and Hygiene
Contactless operation matters in:
- Healthcare facilities: Infection control protocols prohibit shared-surface contact
- Food processing: Hygiene regulations require touchless systems
- Clean rooms: Contamination prevention demands zero-contact verification
- Industrial PPE environments: Workers wearing gloves cannot use fingerprint scanners
Facial recognition, iris recognition, and palm vein scanning operate contactless. Fingerprint and many card-based systems require physical touch, creating hygiene concerns and PPE compatibility issues.
Throughput Speed and User Friction
For facilities with large shift-change workforces—ports, factories, warehouses—a biometric system taking 5+ seconds per person creates bottlenecks that slow throughput and frustrate workers.
Typical transaction speeds:
- Palm vein scanning: Under 2 seconds
- Iris recognition: 2-4 seconds (including positioning time)
- Facial recognition: 1-3 seconds (if no repositioning required)
- Fingerprint scanning: 2-5 seconds (longer if multiple attempts needed due to dirty/wet fingers)
- Voice recognition: 3-6 seconds (including speech prompt and analysis)
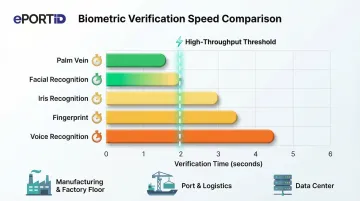
High-volume entry points require systems that process 20-30 people per minute. Only contactless biometrics with sub-2-second verification hit that mark consistently — fingerprint and voice systems fall short when conditions aren't ideal.
Total Cost of Ownership vs. ROI
Upfront hardware cost is only one factor. Organizations should weigh:
- False rejection-driven downtime: Lost productivity when legitimate users are denied
- Administrative overhead: Time spent managing lost credentials, resetting PINs
- Payroll fraud exposure: Buddy punching costs U.S. employers an estimated $373 million annually
- Security incident costs: $4.8 million average per credential theft incident
For most facilities, those hidden costs dwarf the hardware investment — which is why higher-accuracy systems routinely pay for themselves within 3-6 months.
Why Palm Vein Scanning Leads in High-Security Physical Access Environments
For environments where the primary threat is unauthorized physical access—not online account fraud—the evaluation criteria shift decisively toward spoof resistance, contactless operation, and reliability under industrial conditions. Palm vein scanning scores highest across these dimensions compared to fingerprint, facial, and iris alternatives.
The Technical Advantage
With approximately 5 million unique data points per scan, palm vein patterns are shared by no two people—including identical twins. Unlike surface biometrics that can be captured without the person's knowledge (fingerprint residue, facial photo), vein patterns require a living hand and active blood flow to register, making unauthorized replication not feasible with current technology.
Operational Advantages
Those technical properties translate directly into field performance. ePortID's palm vein verification system, developed in partnership with Fujitsu, delivers:
- Sub-2-second verification at 99.99991% accuracy
- True contactless operation — no physical touch required
- Reliable reads regardless of hand condition (dirty, wet, or calloused)
The system uses near-infrared light to detect vein patterns beneath the skin, automatically verifying liveness as part of the scan process. The system requires no separate liveness detection layer, simplifying deployment and reducing failure points.
Business Impact Beyond Security
Palm vein biometrics eliminates buddy punching entirely, creating an indisputable record tied to a living individual. This prevents unauthorized data or facility access and typically pays for itself within 3 to 6 months through:

- Eliminates time theft and buddy punching from payroll
- Cuts administrative overhead — no lost badges to replace or PINs to reset
- Avoids the multi-million dollar costs of preventable security incidents
- Produces audit trails that hold up under regulatory scrutiny
Real-World Application: Biometric Access Control in Critical Infrastructure
Getting biometric technology selection wrong carries real consequences in seaports managing high-security cargo zones, refineries with access-restricted operational areas, financial institutions protecting server rooms, and hospitals guarding pharmaceutical storage. In each case, the cost of a single unauthorized access event—whether from tailgating, credential sharing, or a spoofed biometric—dwarfs the deployment cost of a purpose-built biometric system.
Proven deployments demonstrate measurable impact:
Deployments across sectors confirm that palm vein technology holds up under real security demands:
- The Reserve Bank of India deployed Fujitsu PalmSecure for facility access, citing mandatory liveness detection and fast processing as key selection criteria
- A major Turkish state bank embedded palm vein authentication across 1,500 ATMs for secure, cardless transactions
- A private U.S. hospital enrolled over 5 million patients using palm vein technology, reducing insurance fraud and administrative costs
- Data centers in Germany secured critical zones housing sensitive physical and digital assets with palm vein access control

These results reflect a pattern ePortID has seen across its own deployments in ports, manufacturing plants, and financial institutions. Clients including South Jersey Port Corp., Dow Chemical, Tata Steel, and Thyssen Krupp have implemented contactless palm vein systems drawing on ePortID's 20 years of logistics and security experience with the U.S. Navy, Army JTF, and Port Authorities.
Organizations evaluating biometric access control for high-security facilities can reach ePortID at (215) 627-2651 or info@eportid.com.
Conclusion
Fingerprint and facial recognition serve well in lower-risk, high-volume consumer contexts. Iris recognition fits extreme security scenarios where user friction is acceptable. Palm vein scanning is the strongest choice for physical access control in critical infrastructure settings where accuracy, contactless operation, and spoof resistance must coexist.
A quick look at how each technology maps to real-world demands:
- Fingerprint recognition — best for high-volume, lower-risk environments where cost and familiarity matter most
- Facial recognition — suited to consumer applications and surveillance-integrated workflows with moderate security requirements
- Iris scanning — appropriate for extreme-security scenarios where users accept slower, more deliberate enrollment and verification
- Palm vein scanning — the right fit for facilities where unauthorized access carries safety, financial, or regulatory consequences
Choosing a biometric system comes down to one question: what does a failure cost you? For facilities like data centers, port terminals, and chemical plants — where a single unauthorized entry can trigger safety incidents, regulatory violations, or financial exposure — the performance gap between commodity biometrics and palm vein verification is real and worth quantifying before you commit to a system. Providers like ePortID have deployed palm vein solutions across exactly these environments, from US port authorities to Dow Chemical and Tata Steel, with accuracy rates that commodity alternatives cannot match.
Frequently Asked Questions
What is the most accurate biometric authentication?
Palm vein scanning and iris recognition consistently rank as the most accurate modalities. Palm vein recognition adds the advantage of being contactless and inherently liveness-checked, making it the strongest choice for high-security physical access environments.
What is the difference between biometric verification and biometric identification?
Biometric verification is a 1:1 process, confirming a person is who they claim to be. Biometric identification is a 1:N process, searching a database to determine who an unknown person is. Most physical access control systems use verification.
Is palm vein scanning better than fingerprint scanning for access control?
For high-security environments, palm vein scanning outperforms fingerprint scanning on three fronts: spoof resistance, contactless operation, and reliability when hands are dirty, wet, or worn. Vein patterns can't be lifted from surfaces, which eliminates a primary attack vector for fingerprint systems.
Which biometric technology is best suited for high-security facilities?
Palm vein scanning is widely considered the strongest option for critical infrastructure. Its combination of accuracy, contactless operation, and spoof resistance makes it well-suited to high-threat environments — though the right fit always depends on your specific operational conditions.
Can biometric data be stolen, duplicated, or spoofed?
Surface biometrics like fingerprints and facial images carry higher spoofing risk than internal biometrics. Palm vein patterns require living tissue and active blood flow to register, making unauthorized duplication practically impossible to achieve.
What does "contactless biometric verification" mean, and why does it matter?
Contactless biometrics capture identity data without requiring physical touch. This matters for hygiene in healthcare and food environments, usability with PPE in industrial settings, and reduced wear on hardware in high-throughput facilities.