Introduction
At high-security sites — seaports, data centers, military installations, industrial facilities — traditional credentials create vulnerabilities that operational leaders can no longer ignore. Keycards can be lost, cloned, or shared. PINs can be forgotten or disclosed. Fingerprint scanners pose hygiene risks: a 2021 study of hospital biometric devices found 95–100% showed bacterial growth before cleaning, with pathogens transferring to users' hands at rates exceeding 60% for common viruses and bacteria. Contactless biometrics eliminates these risks by making identity inseparable from the person.
The term gets used broadly, but the operational mechanics behind it rarely get the direct treatment that deployment decisions require. This article breaks down how contactless biometric systems actually verify identity, where each method performs reliably, and where the tradeoffs make a different approach the better call.
TL;DR
- Contactless biometrics verifies identity using unique physical traits — face, iris, palm veins, or voice — without requiring physical contact with sensors
- Each method trades off differently: facial recognition scales fast, iris delivers precision, palm vein resists spoofing, and voice works remotely
- All systems follow a three-phase flow: enrollment, live capture with liveness detection, and template matching
- Performance varies by environment, enrollment quality, and liveness detection — no single modality fits every setting equally
What Is Contactless Biometrics?
Contactless biometrics is the automated verification or identification of a person based on unique physiological or behavioral traits — captured at a distance, without physical contact with any sensor or device.
The technology replaces credentials that can be lost, stolen, shared, or forgotten with something inherent to the individual: a characteristic that cannot be transferred or duplicated. NIST's biometrics program defines the scope to include face, iris, voice, and vein pattern recognition across identity verification applications.
Contactless vs. Touch-Based Systems
The underlying matching logic between both system types is similar. The difference lies in the capture mechanism:
- Touch-based (fingerprint scanners, card readers) require deliberate physical contact with a sensor
- Contactless systems capture biometric data passively or with minimal user action — a glance, a raised palm, a spoken phrase
One Important Distinction
Contactless does not mean remote. The person must still be physically present within sensor range. A palm vein scanner requires the hand held within inches of the device; facial recognition can operate at several meters. Presence is still required — just not touch.
Key Methods of Contactless Biometrics
Four primary modalities dominate real-world deployment. Each uses different sensing technology, captures different biometric data, and suits different environments and security requirements. Organizations may combine modalities (multimodal authentication) to improve accuracy or compensate for environmental limitations.
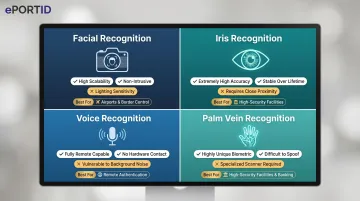
Facial Recognition
Facial recognition uses cameras to capture 2D or 3D images of the face. AI algorithms extract geometric features — distances between key landmarks, contour depth — and create a digital signature matched against stored templates. Modern systems use infrared or structured-light cameras to function across varied lighting and can authenticate users while walking, without requiring them to stop.
Strengths:
- High throughput at entry points
- Wide deployment familiarity
- Works at distance (1–5 meters)
Operational sensitivity:
Performance degrades with face coverings. NIST's 2020 masked-face evaluation tested 89 algorithms: top performers saw false non-match rates (FNMR) rise from 0.3% to 5% with masks; many others degraded to 20–50% depending on mask style and coverage. Extreme lighting variation and significant appearance changes also reduce accuracy.
The TSA currently operates facial comparison technology at approximately 350 U.S. airports, using top-performing algorithms from NIST evaluations for voluntary, touchless identity verification.
Iris Recognition
Iris recognition uses near-infrared (NIR) imaging to capture the unique texture of the iris — a pattern that forms before birth and remains stable throughout life. NIST's IREX VI study confirmed no consistent change in iris texture occurs for at least a decade, which makes it a strong fit for applications requiring persistent identity records over time.
The modality delivers high accuracy and extremely low false-match rates, making it preferred for border control, high-security research environments, and healthcare settings where precision matters more than speed. Modern sensors have expanded capture range considerably, enabling practical contactless operation at greater distances than early systems.
Voice Recognition
Voice recognition analyzes unique vocal characteristics — pitch, cadence, rhythm, and tone — to create a voiceprint for each individual. It operates through standard microphones or phones, making it the only modality suited for remote or mobile authentication: field workers, call center verification, or situations where physical presence at a sensor is impractical.
Key limitations:
- Susceptible to background noise in industrial environments
- Vulnerable to replay attacks if liveness detection is not implemented
- Accuracy varies with recording quality and environmental acoustics
NIST conducts ongoing Speaker Recognition Evaluations (SRE21, SRE24) to benchmark system performance across conversational speech and varied conditions.
Palm Vein Scanning
Palm vein scanning uses near-infrared light to illuminate the hand from below the skin surface. Hemoglobin in the blood absorbs the light, allowing the system to map the unique pattern of veins beneath — a pattern that cannot be observed, copied from a surface, or replicated externally. Fujitsu's PalmSecure technology captures this vein map as the basis for identity verification.
Because only active blood flow produces the vein pattern, a prosthetic, photograph, or severed hand cannot generate a valid reading. This built-in liveness check makes palm vein scanning resistant to the spoofing attacks that compromise surface-based biometrics.
These properties make palm vein scanning the preferred choice for high-stakes environments: seaports, military bases, data centers, refineries, and financial institutions where a spoofed credential is not an acceptable risk.
ePortID's Fujitsu-powered palm vein solution derives identity from approximately 5 million unique reference points, achieving 99.99991% accuracy with verification completing in under 2 seconds — precise enough to distinguish identical twins. With 20 years of experience in logistics and security for the US Navy, Army JTF, and Marine Corps, ePortID deploys this technology for commercial clients including Dow Chemical, Tata Steel, and South Jersey Port Corp.
How Contactless Biometric Verification Works
Regardless of modality, all contactless biometric systems follow the same three-phase process: enrollment, live capture with feature extraction, and template matching leading to an access decision. The system never stores a photograph or audio recording — only an encrypted mathematical template derived from the biometric data.

Phase 1: Enrollment
The user presents their biometric trait one or more times. The system captures multiple samples to account for natural variation, extracts the relevant feature data (geometric landmarks, vein coordinates, voiceprint), and converts it into an encrypted template stored in the system database.
Enrollment quality directly affects long-term performance. Poor capture conditions during enrollment — inadequate lighting, incorrect positioning, motion blur — create persistent false rejection issues that degrade the user experience and erode confidence in the system.
Best-practice enrollment protocols include:
- Controlled environment with consistent lighting and positioning
- Multiple capture attempts to ensure sample quality
- Immediate feedback to the user if initial samples are insufficient
- Standardized processes across all enrollment stations
Phase 2: Live Capture and Feature Extraction
When a person approaches the sensor, the system captures live biometric data in real time. AI algorithms process the raw input and extract the same feature types used during enrollment. At the same time, liveness detection algorithms verify that the input comes from a physically present person — not a photograph, mask, recording, or synthetic substitute.
Liveness detection is a mandatory security layer. ISO/IEC 30107-3 defines Presentation Attack Detection (PAD) testing principles and methods to validate that biometric systems can resist spoofing attempts. Organizations deploying contactless systems should require PAD certification from vendors.
Phase 3: Template Matching and Access Decision
The live feature set is compared against the stored template using a matching algorithm that generates a similarity score. If the score meets or exceeds the configured threshold, access is granted; if not, it is denied. The system logs the outcome — including timestamp, location, and match score — creating an immutable audit record.
The threshold can be adjusted to balance security stringency against false rejection rates depending on the deployment context. NIST defines standard metrics for evaluating system performance, including:
- False Accept Rate (FAR) — the rate at which unauthorized users are incorrectly granted access
- False Non-Match Rate (FNMR) — the rate at which legitimate users are incorrectly denied access
Configuring the right threshold for your environment means balancing these two metrics against your security requirements.
Where Contactless Biometrics Is Applied
Contactless biometrics delivers the most operational value when environments share at least one of three characteristics:
- High throughput: Many people accessing a checkpoint quickly, where delays create bottlenecks
- Hygiene sensitivity: Shared touch surfaces create contamination risk
- High-security stakes: Credential sharing or unauthorized access carries serious consequences
Industry adoption concentrates in environments where these conditions overlap.
Critical Infrastructure and Industrial Sites
Seaports, power stations, oil refineries, military bases, and data centers require certainty about who is accessing restricted zones, with zero tolerance for shared or transferred credentials. Palm vein and iris scanning are the preferred scanning methods given the accuracy requirements and the common use of gloves or protective equipment.
ePortID's SeaPortPass solution integrates contactless palm vein biometric scanning with real-time TWIC (Transportation Worker Identification Credential) verification required under the Maritime Transportation Security Act. The system verifies TWIC cards against the TSA Cancelled Card List in real time, ensuring only active, authorized personnel access secure port areas.

NERC CIP-006-6 physical security standards require two or more different access controls for High Impact bulk electric systems where feasible. Biometrics fulfill this requirement while eliminating the risks of shared credentials or buddy punching common with card-only systems.
Healthcare and Regulated Facilities
Healthcare faces a dual driver: hygiene (shared fingerprint scanners become contamination vectors) and accuracy (misidentification of patients or staff carries direct safety consequences). Palm vein and iris scanning allow staff to authenticate without removing gloves.
HIPAA physical safeguards require policies and procedures for facility access control, workstation security, and device/media controls to protect electronic protected health information (ePHI). Contactless biometrics provides the identity assurance and audit logging needed for compliance.
The compliance pressure is real: 746 breach incidents in 2023 alone affected over 289 million individuals in 2024, making identity verification a patient safety issue, not just an IT concern.
Airports, Border Control, and Transportation
Facial recognition is deployed at boarding gates and passenger processing checkpoints for high-throughput, fast authentication. Iris recognition is used at immigration and border control where positive identification of each individual must hold up to legal and national security scrutiny. DHS/CBP's 2025 Final Rule authorizes universal facial biometric collection from noncitizens at entry and exit, making the programs permanent and removing prior exemptions.
These environments demonstrate the high-throughput capability of modern contactless systems, processing thousands of travelers per hour without physical contact or bottlenecks.
Enterprises, Financial Institutions, and Data Centers
Preventing unauthorized access to server rooms, trading floors, executive areas, and financial systems requires frictionless authentication where the cost of a breach is high but daily access volumes demand speed. Multimodal approaches — face at main entry, palm vein at restricted zones — are common.
ePortID's ePortPass solution combines Fujitsu F-Pro palm vein scanners with Power-over-Ethernet door control units, eliminating the need for licensed electricians and enabling rapid deployment using existing network infrastructure. Integration via Wiegand or OSDP protocols allows connection to existing access control systems without complete replacement.
Key Factors That Affect Performance and Accuracy
Several primary variables determine whether a contactless biometric deployment succeeds or underperforms in practice:
Environmental conditions:
Ambient lighting directly affects facial and iris recognition accuracy. Background noise degrades voice recognition. Palm vein scanning operates in the near-infrared spectrum beneath the skin surface, making it the least environmentally sensitive modality.
Enrollment quality:
The accuracy of every future verification depends on how well the initial biometric samples were captured. Best-practice enrollment protocols include:
- Controlled capture environments with consistent lighting and positioning
- Multiple capture attempts to establish a reliable baseline template
- Immediate feedback to users during the enrollment process
- Standardized procedures across all enrollment stations
Liveness detection sophistication:
The maturity of the anti-spoofing layer determines resistance to presentation attacks. ISO/IEC 30107-3 defines PAD testing methods and metrics. This varies significantly across vendors and should be a primary evaluation criterion. Recent fingerprint spoofing research has demonstrated spoof success rates up to 95.2% with silicone replicas against capacitive and optical sensors, highlighting the importance of robust PAD.
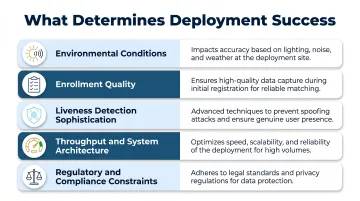
Throughput and system architecture:
High-traffic entry points require systems capable of processing multiple authentications per minute without queuing. Whether processing occurs at the edge or in the cloud affects latency and failure-mode behavior.
Regulatory and compliance constraints:
Data protection laws — including GDPR Article 9, CCPA/CPRA, and the HIPAA Security Rule — and sector-specific standards such as TWIC for maritime and FedRAMP for federal systems all impose requirements on template storage, retention periods, and audit logging. These compliance obligations directly shape system architecture decisions.
Common Misconceptions and Limitations
"Contactless biometrics is inherently less secure than touch-based systems."
This is incorrect. Well-implemented contactless systems — particularly those using subsurface traits like palm veins — are more resistant to spoofing than fingerprint scanners. Foundational research demonstrated artificial gummy fingers could bypass fingerprint systems, and recent studies confirm spoof success rates exceeding 90% with gelatin and silicone replicas. Security depends on the modality chosen, liveness detection quality, and encryption practices — not on whether the sensor requires contact.
"Any contactless modality works in any environment."
Not quite. Each modality has real-world constraints:
- Facial recognition degrades with face coverings, extreme lighting, or significant appearance changes
- Voice recognition fails in high-noise industrial settings
- Iris recognition requires precise user positioning
Organizations should evaluate modality fitness against their specific physical environment before committing to a deployment.
When contactless biometrics may not be the right fit:
- Very low-volume access points where deployment cost cannot be recovered
- Environments where workers wear full-face PPE with no secondary modality available
- Use cases requiring fully remote authentication (contactless still requires physical presence within sensor range)
The right modality is the one that matches your environment, user population, and threat model — not simply the most familiar option.
Conclusion
Contactless biometrics replaces physical credentials — which can be lost, shared, forgotten, or stolen — with identity characteristics that are inherent, unique, and non-transferable. The technology's value is realized when the right modality is matched to the right environment, with proper enrollment practices and appropriate liveness detection in place.
For security and operations managers at critical facilities, operational understanding matters more than concept familiarity. A well-specified deployment — one matched to the environment, with correct enrollment and liveness controls — outperforms a hastily adopted system every time. The gains contactless biometrics delivers are real, but they follow from correct application, not from the technology alone.
Frequently Asked Questions
What is contactless biometrics?
Contactless biometrics is identity verification using unique physical or behavioral traits captured without touching a sensor. The capture method differs from touch-based systems (cameras, infrared sensors, or microphones replace fingerprint pads), but the underlying matching logic works the same way.
What is multimodal biometric authentication?
Multimodal biometric authentication uses two or more biometric modalities together — such as face plus palm vein — to increase accuracy, reduce false rejection rates, or compensate when a single method is limited by environmental conditions like face coverings or gloves.
How does a biometric card work?
A biometric card stores the holder's biometric template on the card itself. When used, the card captures a live sample at the reader and performs the match on-card rather than sending data to a central server.
How does palm vein authentication work?
A near-infrared sensor illuminates the palm, causing hemoglobin to absorb the light and reveal the unique vein pattern beneath the skin's surface. That pattern converts to an encrypted template matched against the stored record. Liveness detection is built in — only active blood flow generates a readable result.
Is palm vein recognition safe?
Palm vein recognition is one of the safest biometric options available. The vein pattern is internal, so it cannot be lifted from surfaces or photographs. Liveness detection blocks spoofing attempts, and biometric data is stored as an encrypted mathematical template rather than a raw image, protecting both physical security and privacy.