
Introduction
In high-security environments — seaports, refineries, data centers, military bases — a lost badge or shared RFID card isn't just an inconvenience. It's a documented security incident. A Florida case prosecuted in 2026 involved a defendant possessing approximately 450 fraudulent access devices, resulting in victim losses between $250,000 and $550,000.
Federal contractors face the same exposure. Consolidated Nuclear Security LLC paid $18.4 million in 2024 to settle timecard fraud allegations at a nuclear facility — showing that credential-based time systems carry real compliance and financial risk.
Both systems solve attendance tracking. But the cases above point to a sharper question: are you authenticating an identity, or authenticating a credential?
The wrong choice exposes your organization to time theft, payroll leakage, unauthorized access, and audit failures. This guide breaks down how each system works, where each fits, and which one belongs in your operation.
TL;DR
- Biometric time clocks verify identity using unique physical traits (fingerprint, face, palm vein); RFID clocks verify possession of a card or fob, with no way to confirm who is actually holding it
- Biometric systems eliminate buddy punching entirely; RFID reduces it but remains vulnerable to card sharing
- RFID costs less upfront; biometric systems deliver stronger ROI — typically recovering investment in 3 to 6 months in high-fraud environments
- Biometric systems check for liveness during verification and reach accuracy rates of 99.99991% — making them the appropriate standard for regulated industries and high-security facilities
- RFID works well for lower-risk environments where convenience matters more than identity certainty — particularly when combined with PIN dual-authentication
What is a Biometric Time Clock?
A biometric time clock authenticates employee identity by measuring unique physiological characteristics (fingerprints, facial geometry, iris patterns, or palm vein networks) and matching them against encrypted stored templates. Unlike card-based systems — which verify that a credential is present — biometric systems verify that the person is present. The identifier cannot be lost, forgotten, shared, or duplicated.
This distinction matters operationally. Biometric systems create an indisputable record of who was present, when, and where — critical for payroll accuracy, compliance audits, and access control in regulated environments.
Primary Biometric Modalities
Four primary biometric technologies power modern time clocks:
Fingerprint Scanning
The most common and affordable modality. Proven technology with broad vendor support, though vulnerable to dirty or damaged hands and spoofing via lifted prints.
Facial Recognition
Contactless and high-throughput. Ideal for environments requiring speed and hygiene, though lighting conditions and mask-wearing can affect accuracy.
Iris/Retina Scanning
Highest accuracy, best suited for top-security environments. Requires close proximity and controlled lighting, making it less practical for high-volume applications.
Palm Vein Scanning
ePortID's palm vein technology — built on Fujitsu's PalmSecure F-Pro scanner — generates identity from 5 million unique data points beneath the skin. The vein pattern cannot be replicated even by identical twins. The system achieves 99.99991% accuracy, verifies in under 2 seconds, and includes liveness detection during every scan. Because the technology detects blood flow beneath the skin using infrared light, spoofing or proxy enrollment is impossible — the system inherently confirms the person is alive and present.

Core Operational Benefits
Biometric time clocks deliver measurable advantages:
- Eliminate buddy punching — no shareable credential means no proxy clock-ins
- Automate time records to reduce payroll processing costs and manual errors
- Generate auditable logs that support compliance with OSHA 29 CFR 1904, HIPAA 45 CFR 164.312, and NERC CIP-004-7
- Link time tracking with door control systems to block unauthorized facility entry
Use Cases of Biometric Time Clocks
Biometric time clocks fit best in environments where identity certainty is non-negotiable. These include seaports, airports, power stations, oil rigs, refineries, data centers, server rooms, military bases, pharmaceutical labs, and financial institutions. In these settings, the consequence of a misidentified clock-in extends beyond payroll error to potential safety or security breach.
The Financial Scale of Time Theft
The financial exposure is substantial across industries of all sizes:
- Buddy punching costs U.S. employers an estimated $373 million annually, affecting 75% of businesses
- Time theft accounts for an average loss of 2.2% of gross payroll, per Nucleus Research
- The average employee steals 4 hours and 5 minutes per week, according to the American Payroll Association
- 16% of employees admit to clocking in for a colleague

For organizations in critical infrastructure or regulated industries, biometric time clocks close this gap while generating audit-ready records that card-based systems simply cannot produce.
What is an RFID Time Clock?
An RFID (radio-frequency identification) time clock reads a unique code stored on a badge, card, or key fob when held near a reader. The system logs the code — not the individual — as present. RFID authenticates possession of a credential, not the identity of the person holding it.
How RFID Systems Work
Employees carry physical tokens programmed with unique IDs. When held near a reader, the token's signal is captured and a timestamp is recorded — typically within sub-second range. Many organizations deploy RFID cards for both time tracking and physical access control, making them a natural fit for multi-function badge programs.
Passive vs. Active RFID:
- Passive tags draw power from the reader's electromagnetic field and work at short range (0–4 inches for HF cards, up to 30 feet for UHF)
- Active tags contain a built-in battery and transmitter, broadcasting signals over 100–300 feet without needing a reader to initiate contact
Where RFID Adds Value
RFID systems offer practical advantages in specific environments:
- Fast clock-in throughput — sub-second scan times
- Low enrollment friction — issue a card, no biometric enrollment required
- Easy credential replacement — lost cards can be deactivated and reissued quickly
- Legacy infrastructure compatibility — works with existing Wiegand-based access systems
- Lower initial hardware cost — readers and cards cost less than biometric terminals
That trade-off — speed and simplicity against identity assurance — is where RFID and biometric systems diverge most sharply.
Use Cases of RFID Time Clocks
RFID time clocks work well in environments where operational speed matters more than strict identity verification. Common deployments include:
- Large retail operations — high shift volumes, fast employee throughput at clock-in
- Hospitality venues — hotels and restaurants with predictable rosters and low fraud incentive
- Mid-sized manufacturing plants — structured shifts where badge loss is infrequent
- Corporate offices — low-security environments focused on attendance logging over access control
In these settings, RFID delivers reliable convenience. The trade-off is identity assurance — the system confirms a valid card was presented, not who presented it.
Why RFID Can't Stop Credential Sharing
RFID has no way to confirm that the person presenting a card is its authorized holder. That gap creates a direct path to buddy punching. Research shows that 16% of employees admit to clocking in for a colleague, and companies moving from card-based scanners to biometric systems increased payroll accuracy by at least 50%.
The hardware itself adds another layer of risk. Security researchers in 2024 exposed a backdoor in millions of widely deployed MIFARE Classic RFID cards, enabling near-instant cloning. Legacy 125 kHz HID Prox cards carry the same vulnerability — off-the-shelf tools like the Proxmark3 can duplicate them in seconds.
Where credential fraud carries financial or safety consequences — ports, data centers, healthcare facilities — RFID alone leaves too much to trust.
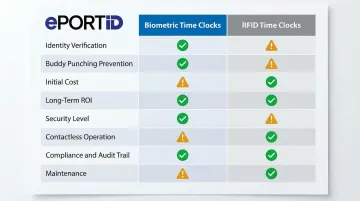
Biometric vs RFID Time Clocks: Quick Comparison
The table below maps eight decision-critical dimensions side by side so you can match each system's strengths to your environment at a glance.
| Dimension | Biometric Time Clocks | RFID Time Clocks |
|---|---|---|
| Identity Verification | Verifies the person | Verifies the credential |
| Buddy Punching Prevention | Eliminated entirely | Reduced but not eliminated |
| Initial Cost | Higher ($1,500–$5,000+ setup) | Lower ($500–$2,000 setup) |
| Long-Term ROI | Stronger in high-fraud/high-compliance environments | Sufficient for environments with low fraud risk and basic compliance needs |
| Security Level | High, with liveness detection in advanced systems | Moderate, susceptible to card sharing/cloning |
| Contactless Operation | Fully contactless (palm vein/facial) | Contactless but credential-dependent |
| Compliance & Audit Trail | Identity-linked records ideal for regulated industries | Logs credential events, weaker for strict audits |
| Maintenance | Minimal; no physical credentials to replace or reissue | Ongoing card replacement and issuance costs |
Biometric vs RFID: Which is Right for Your Operation?
The decision framework begins with a single question: Are we authenticating identity, or authenticating a credential?
When to Choose Biometric
Choose biometric if:
- Your operation sits in critical infrastructure, healthcare, financial services, government contracting, or defense — where identity fraud carries real consequences
- Regulations apply — OSHA 29 CFR 1904, HIPAA 45 CFR 164.312, NERC CIP-004-7, or FAR 52.216-7 mandate strict audit controls and unique user identification that shared RFID badges can't reliably provide
- Touch-free punch-in is required for infection control — common in healthcare, food processing, and clean-room environments
- Unauthorized access to hazardous materials or sensitive data creates direct safety or liability exposure
Total Cost of Ownership:
RFID carries lower upfront hardware costs but ongoing expenses from card replacement, re-issuance, and payroll leakage from buddy punching. An independent IDC study of biometric time clocks revealed an average ROI of 537% with a payback period of less than 5 months, saving $59,250 per 100 users annually.
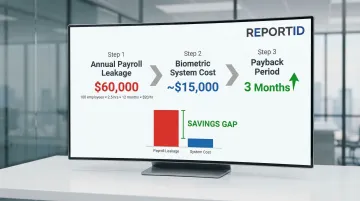
Example Scenario (100-Person Shift Operation):
Assume average wage of $20/hour. If each employee steals 2.5 hours per month via buddy punching, annual payroll leakage = 100 employees × 2.5 hrs/month × 12 months × $20/hr = $60,000. Biometric system cost: ~$15,000. Payback period: 3 months.
When to Choose RFID
Choose RFID if:
- Sub-second clock-in speed is non-negotiable and upfront hardware cost is the primary constraint
- Turnover is low, culture is strong, and fraud risk is genuinely minimal
- Existing badge-access infrastructure is already deployed and re-enrollment at scale isn't practical
- The facility is a standard office environment without sensitive data, regulated assets, or critical infrastructure exposure
The Hybrid Option
Some operations deploy RFID for general facility access and biometric for sensitive zones or payroll punch points — combining card-based efficiency with identity certainty at the checkpoints that carry the most risk.
ePortID supports this configuration directly: RFID readers integrate with palm vein scanners via Wiegand or OSDP protocols, enabling two- or three-part authentication (biometric + RFID + PIN) wherever the environment demands it.
Real-World Applications in High-Security Environments
ePortID has deployed biometric time and access solutions for clients including South Jersey Port Corp., Dow Chemical, Tata Steel, Thyssen Krupp, and Fiserv: environments where workforce identity verification carries direct implications for safety, regulatory compliance, and physical security. That experience extends to 20 years supporting identity verification for the U.S. Navy, Army JTF, Marine Corps, and Port Authorities.
The Challenge: Credential-Based Security Gaps
Consider a representative scenario at a refinery or industrial port facility:
RFID badge systems allow employees to clock in for absent colleagues. A shared badge grants unauthorized personnel access to hazardous zones. Payroll records show workers on-site during incidents when they were not physically present — and compliance auditors demand identity-linked access logs that card-based systems cannot produce.
The operational consequences are direct:
- Payroll fraud and unauthorized overtime costs
- Unauthorized zone access creating safety and security exposure
- Audit failures under OSHA, NERC CIP, or contractor fraud regulations
- No verifiable proof of who accessed critical infrastructure
The Solution: Biometric Identity Verification
Replacing or augmenting RFID with biometric palm vein scanning addresses the identity verification gap:
- Indisputable record tied to the individual — eliminates buddy punching and credential sharing
- Prevents unauthorized access to secure zones — only enrolled personnel can authenticate
- Generates audit-ready logs — compliance reviews receive identity-linked entry records, not just card swipes
- Reduces payroll processing time — automated, accurate records eliminate manual reconciliation

ePortID's contactless palm vein technology verifies identity in under 2 seconds with 99.99991% accuracy. The tamper-proof records it generates support compliance with OSHA timekeeping requirements, HIPAA unique user identification mandates, and NERC CIP personnel access controls.
Organizations in critical infrastructure, energy, ports, or regulated industries can contact ePortID at info@eportid.com or 215-627-2651 to discuss how contactless palm vein technology can be configured for their specific environment.
Conclusion
RFID time clocks are a practical, cost-efficient option when speed, credential convenience, and lower upfront investment are the priority — and when workforce stability makes credential sharing an acceptable risk.
Biometric time clocks are the right call when identity certainty, audit integrity, and eliminating time theft are non-negotiable. Here's a simple way to frame the decision:
- Choose RFID if your workforce is stable, your environment is low-risk, and budget constraints are real
- Choose biometrics if you operate in a regulated, high-security, or critical infrastructure environment where credential sharing carries serious consequences
- Choose palm vein biometrics specifically if contactless verification, liveness detection, and near-zero false acceptance rates are required
For seaports, power stations, data centers, and similar environments, the stakes go beyond payroll accuracy. You need to know — with certainty — who entered a facility, which zone they accessed, and exactly when. A card or fob tells you a credential was used. Biometric verification tells you a person was there. That distinction matters when compliance, liability, or physical security is on the line.
Frequently Asked Questions
What is the difference between RFID and biometric?
RFID verifies possession of a card or fob (credential-based), while biometric systems verify the physical identity of the person using unique physiological traits. RFID authenticates what you carry; biometrics authenticate who you are.
What type of clock is the most accurate?
Biometric time clocks — particularly palm vein and iris scanning systems — offer the highest accuracy. ePortID's palm vein technology achieves 99.99991% accuracy, compared to RFID which can be circumvented by credential sharing.
Can RFID time clocks prevent buddy punching?
RFID systems reduce but do not eliminate buddy punching, since any employee can present another's badge. Biometric systems eliminate buddy punching entirely because physical traits cannot be transferred.
Are biometric time clocks more expensive than RFID systems?
Biometric systems carry higher upfront costs than RFID, but the total cost of ownership often favors biometric once time theft is factored in. Payroll savings and fraud prevention typically recover the investment within 3 to 6 months.
What industries benefit most from biometric time clocks?
Critical infrastructure sectors benefit most — seaports, airports, power stations, oil rigs, refineries, data centers, hospitals, financial institutions, and military installations — where identity certainty, compliance audit trails, and access control converge.
Is biometric data stored securely in biometric time clock systems?
Reputable systems store encrypted mathematical templates rather than raw images, so stored data cannot be reconstructed into the original biometric. Confirm your vendor uses encrypted storage and complies with GDPR, CCPA, and applicable state biometric privacy laws.


