Introduction
Since March 2020, the U.S. Chemical Safety and Hazard Investigation Board (CSB) has received reports of over 555 chemical incidents across 43 states, with 120 incidents occurring in fiscal year 2025 alone. CSB data covering 94 serious incidents documented 16 fatalities, 75 serious injuries, and over $4.5 billion in property damage. Each incident represents a chain reaction that begins with a single point of failure.
For chemical facilities, that failure point is often the gate. An unauthorized entry can trigger chemical exposure, facility lockdowns, regulatory penalties, and community safety events that cost far more than a robust access control system. In one 2020 incident, perpetrators cut through a perimeter fence at an Ohio agricultural facility to steal anhydrous ammonia — causing a hazardous leak that injured first responders and forced an extended shutdown.
This guide covers what effective gate security looks like for chemical facilities: from access control technologies and perimeter design to regulatory compliance and visitor management protocols.
TL;DR
- Gate failures at chemical facilities allow unauthorized access to hazardous materials — the consequences are irreversible
- CFATS lapsed in 2023, but liability and insurance exposure remain; self-imposed equivalent standards are now table stakes
- Crash-rated barriers, anti-tailgate portals, and electronic access control must operate as one integrated system
- Biometric verification eliminates credential sharing — the most common physical access control failure in industrial facilities
- Zone-based access policies and time-bound contractor credentials mark the line between compliant and genuinely secure
Why Gate Security & Access Management Can't Be an Afterthought at Chemical Facilities
Chemical facility gates are the primary control layer between the public and hazardous materials, proprietary processes, and critical infrastructure. A breach at a chemical plant gate carries consequences that no office building breach ever would.
The risks are irreversible: chemical exposure, environmental contamination, and community-wide safety emergencies that can't be undone after the fact.
Gate security must address three core threat categories:
External intrusions include trespassers, vehicle ramming attacks, and forced entry attempts. The Mineta Transportation Institute documented 85 vehicle ramming attacks in the United States since 2012, making this a proven threat vector.
Insider threats encompass unauthorized re-entry by former employees, credential sharing among shift workers, and access outside permitted zones. According to ASIS International's 2023 Access Control Research Report, 61% of security professionals experienced tailgating or piggybacking incidents in the past six months, while 38% reported card or credential sharing.
Third-party risks involve unvetted contractors, delivery personnel with unmanaged access, and visitors who bypass proper protocols. OSHA Process Safety Management violations frequently stem from facilities failing to control contractor entrance, presence, and exit in covered process areas.

Regulatory Framework: What Chemical Facilities Are Required to Do
Multiple regulatory frameworks govern gate and access security at chemical facilities. The Chemical Facility Anti-Terrorism Standards (CFATS) statutory authority expired on July 28, 2023, meaning CISA can no longer enforce compliance or conduct inspections. However, CFATS Risk-Based Performance Standards remain an industry benchmark — particularly RBPS 1 (Restrict Area Perimeter), RBPS 2 (Secure Site Assets), and RBPS 3 (Screen and Control Access).
Three additional regulatory mandates directly address gate and access control:
- OSHA PSM (29 CFR 1910.119) requires facilities to "develop and implement safe work practices to control the entrance, presence and exit of contract employers and contract employees in covered process areas." This is a regulatory mandate with citation authority — not a guideline.
- EPA Risk Management Program (40 CFR Part 68) mirrors OSHA PSM requirements, mandating equivalent control over contractor access in covered areas.
- Maritime Transportation Security Act (MTSA) applies to facilities near waterways, requiring access control, restricted area designation, and TWIC credential verification.
CFATS lapsing doesn't remove operational or liability risk — it increases the need for facilities to self-impose equivalent standards. When an incident occurs, regulators and insurers will review gate entry records to determine liability exposure. Compliance documentation — access logs, audit trails, visitor records — becomes your primary defense.
The Stakes of Getting It Wrong
Inadequate gate security carries concrete consequences. In 2011, OSHA issued a Serious citation to ExxonMobil's Baton Rouge refinery for violating 29 CFR 1910.119(h)(2)(iv) — the facility failed to account for contract employees during demolition work.
OSHA inspectors found that two contract employees had left the permitted work area but remained unaccounted for within the unit. No tracking. No record.
The consequences extend beyond citations. Facility shutdown, EPA enforcement actions, OSHA fines, and reputational damage follow security failures. EPA RMP data from 2016-2020 estimated average annual onsite damages of $434 million and offsite damages of $43.3 million from chemical incidents. When investigators trace an incident back to inadequate perimeter controls, liability exposure can threaten the facility's operational future.
Physical Gate Infrastructure: Your First Line of Defense
Physical gate infrastructure forms the "hardened shell" of chemical facility security. Electronic systems and credentials are only as strong as the physical barriers backing them — a vehicle that bypasses the gate entirely renders every credential check moot.
Gate Types and Applications
Crash-rated vehicle gates are essential for primary entry points handling heavy truck traffic. These gates must meet ASTM F2656 certification standards, which test barriers against 15,000-pound truck impacts at 30 mph (M30), 40 mph (M40), or 50 mph (M50).
Penetration ratings define how far the vehicle payload travels past the barrier: P1 (under 3.3 feet), P2 (3.3–23 feet), or P3 (23–98 feet). For facilities near public roads or with high tanker traffic, M50-P1 rated barriers offer the strongest protection.
Beyond vehicle gates, three additional barrier types complete the physical layer:
| Barrier Type | Primary Function | Key Consideration |
|---|---|---|
| Anti-tailgate turnstiles / mantrap portals | Enforce individual pedestrian authentication | Waist-high turnstiles offer minimal protection; full-height or interlocking mantraps are required for high-security zones |
| Bollards and crash beams | Absorb and dissipate vehicle kinetic energy | ASTM F2656-certified bollards serve as the final barrier against vehicle ramming |
| Perimeter fencing with intrusion detection | Detect and alert on unauthorized fence breaches | After perpetrators cut through a fence at an Ohio facility to reach an ammonia tank, the leak that followed injured first responders on scene |

ASIS International guidelines note that rotary gates and mantraps force individual authentication — eliminating the assumption that a badge seen once covers the whole group.
Preventing Tailgating at the Gate Zone
The gate zone itself must be designed to prevent tailgating — one unauthorized person following an authorized vehicle through an opening. Physical design features address this vulnerability:
- Vehicle airlocks create a controlled space where only one vehicle can enter at a time
- Sally ports use sequential gates that prevent the second gate from opening until the first closes
- Sensor-triggered alerts flag when more than one vehicle or person moves through a controlled opening
- Serpentine road alignment calms traffic approaching control points and prevents ramming acceleration
CISA's Vehicle Ramming Self-Assessment Tool recommends combining passive barriers (bollards) with active barriers (gates) at perimeter control points to create layered physical defense.
Access Control Systems for Chemical Facility Gates
Selecting the right access control technology requires matching the credential type to the risk level of the entry point and the population using it. Not all credentials offer equal security.
Credential Hierarchy: Weakest to Strongest
PIN codes represent the weakest option. They're easily shared, offer no identity verification, and leave no audit trail linking a person to an access event.
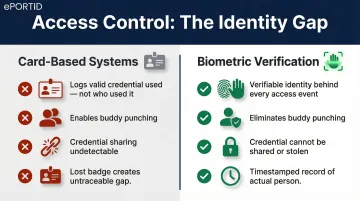
Proximity cards and key fobs improve on PINs but can be lost, stolen, or shared between workers. The 2023 ASIS Access Control Research Report found 38% of facilities experienced card or credential sharing incidents. A lost badge creates an untraceable security gap.
Mobile credentials tie access to a device rather than a person. While better than cards, devices can still be shared or accessed by unauthorized users.
Biometric systems represent the highest standard. Unlike cards or codes, biometric credentials cannot be shared between workers, cannot be forgotten, and cannot be duplicated. They verify the person, not just the credential.
Why Biometrics Eliminate the Core Vulnerability
For facilities managing rotating shifts and large contractor workforces — populations where credential sharing is common — biometrics eliminate the vulnerability that other credential types leave open. Traditional systems log that a valid credential was used, but biometric verification creates an indisputable record of who actually accessed the facility.
ePortID's contactless palm vein scanning technology is designed specifically for high-security gate environments. Key system specs include:
- Derives identity from over 5 million data points unique to each individual
- Achieves 99.99991% accuracy and verifies in under 2 seconds
- Checks for liveness using low infrared light to confirm active blood circulation — preventing spoofing with photographs or replicas
- Fully contactless, keeping throughput fast in outdoor gate environments
Because no two people share the same vein pattern — not even identical twins — the credential cannot be duplicated, shared, or stolen.

Commercial clients including Dow Chemical, Tata Steel, and Thyssen Krupp have deployed palm vein scanning in industrial contexts where credential sharing, lost badges, and "buddy punching" create security gaps that traditional card systems cannot address.
Role-Based Access Control at the Gate
Biometrics only deliver their full value when paired with role-based permissions. Not every worker should reach every area at every hour. Gates and internal checkpoints should be configured so that a delivery driver's credential only opens the loading dock gate, while a process engineer's credential opens the production zone. Both access events are logged with a timestamped identity record — not just a generic badge scan.
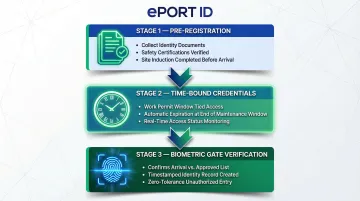
Time-bound credentials for contractors add another layer. A contractor receives access that automatically expires at the end of their four-hour maintenance window. Real-time alerts notify security if someone attempts to access the wrong door or enters outside their authorized timeframe.
Integrating Access Control with Video Surveillance
Role-based access logs are stronger when corroborated by video. Linking gate reader events to camera feeds means the system both verifies the credential and captures visual confirmation of who physically entered.
This integration is essential for compliance auditing and incident investigation. Regulators reviewing an event want more than a system log — they want visual proof that the authorized person actually walked through the gate.
Managing Access for Employees, Contractors, and Visitors
Employees, contractors, and visitors represent three distinct risk profiles at the chemical facility gate and should be managed with separate workflows.
Employee Access
Employees receive verified credentials with role-based permissions tied to their job functions. Access rights are modified when job roles change and revoked immediately upon termination. Real-time alerts flag when former employees attempt access after separation.
Contractor Access
Contractors pose specific risks. They arrive in large, varied groups, may work at multiple sites, and are less familiar with facility hazards. Three controls address these risks before a contractor ever reaches the gate:
- Time-bound credentials tied to the work permit window — a four-hour maintenance credential expires automatically when the window closes
- Pre-registration workflows that collect identity documents, safety certifications, and site induction completion before arrival
- Biometric gate verification that removes the ambiguity of "who actually showed up" versus who was on the approved list
Industry best practices suggest establishing dedicated contractor gates to manage influx during shift changes. For example, facilities often designate separate gates for construction contractors versus general employees, ensuring proof of safety orientation and negative drug screens before entry.
Visitor Management
Visitors should be pre-registered, escorted in high-risk zones, and logged with every gate entry and exit recorded. A detailed audit trail documents when visitors entered, where they went, how long they stayed, and when they exited.
Credential Lifecycle Management
"Orphaned credentials" — active access rights for people who no longer work at the facility — remain one of the most preventable security failures at chemical facilities. Credential lifecycle management requires:
- Issue credentials at onboarding with appropriate, role-specific permissions
- Update credentials immediately when job roles change
- Revoke access on the day of termination or contract completion — not days later
- Run quarterly audits to catch and deactivate any orphaned credentials that slipped through
Common Chemical Facility Gate Security Mistakes — and How to Address Them
Treating Gate Security as a One-Time Installation
Facilities that install access control systems but skip regular audits, software updates, and hardware inspections accumulate risk silently. A credential that should have been revoked six months ago remains active. An outdoor gate reader damaged in a storm has been bypassed with a prop. The consequence isn't just security exposure — it's compliance liability when regulators review access logs after an incident.
Solution: Implement minimum annual formal audits with quarterly credential reviews. Conduct an immediate review following any security incident, personnel change, or system update.
Relying on Single-Layer Credentials for All Entry Points
Facilities that issue proximity cards to all personnel and contractors without higher-assurance verification for high-risk zones create a flat security model. One lost badge compromises the entire facility.
Solution: Implement zone-based credential hierarchies. Require stricter authentication as personnel move deeper into the facility. Loading dock access may use card credentials, but process areas require biometric verification.
Underestimating the Insider Threat
Chemical facilities with large headcounts and shift rotations are particularly vulnerable to insider misuse. Card-based systems only confirm a valid credential was used — not who used it. Common behaviors that go undetected include:
- One worker badging in for another ("buddy punching")
- Shift workers passing credentials between each other
- Contractors accessing zones outside their permitted area
Solution: Biometric verification makes the identity behind the access event verifiable. Time and attendance systems using palm vein scanning eliminate buddy punching, creating a verified, timestamped record of who actually clocked in.
Missing the Integration Imperative
Effective gate security is an integrated, continuously managed system — not a one-time product purchase. Physical barriers, electronic access control, video surveillance, and audit procedures must operate as a unified whole.
Solution: Assign ownership of access management as an ongoing operational function. Schedule reviews when the workforce changes, regulations update, or new threat intelligence emerges — not only after an incident has already occurred.
Frequently Asked Questions
What regulations apply to gate security at chemical facilities?
CFATS lapsed in July 2023 but its Risk-Based Performance Standards remain industry best practice. OSHA PSM (29 CFR 1910.119) and EPA RMP (40 CFR Part 68) mandate control over contractor entrance, presence, and exit. MTSA applies to waterfront facilities, and even without a federal mandate, facilities remain liable for incidents linked to access control failures.
What is the most secure type of access control for a chemical facility gate?
Biometric systems — particularly contactless palm vein scanning — offer the highest assurance because credentials are tied to a person's unique physiology, cannot be shared or stolen, and verify liveness. Card-based systems, by contrast, create an untraceable gap the moment a badge is lost or shared.
How do you prevent tailgating at a chemical facility gate?
Use vehicle airlocks, anti-tailgate portals for pedestrians, and sensor-triggered alerts that flag when more than one person or vehicle moves through a controlled opening. Require individual authentication for every person — one credential never grants passage for a group.
How should contractor and visitor access be managed at a chemical plant gate?
Implement pre-registration workflows, time-bound credentials, and escort requirements for high-risk zones. Gate-level identity verification should confirm each presenter matches the credentialed individual on record.
How often should chemical facility access control systems be audited?
Conduct annual formal audits with quarterly credential reviews to identify orphaned or over-permissioned credentials. Perform immediate review following any security incident, personnel change, or system update.
Can biometric gate readers function reliably in outdoor industrial environments?
Modern contactless biometric systems like palm vein readers are designed for outdoor and industrial deployment, operating in temperatures from -25°C to +80°C (-13°F to +176°F). They verify identity in under two seconds without creating bottlenecks, fast enough to avoid bottlenecks at busy gates.