The security gap is real and measurable. 97% of US public schools controlled building access during school hours according to the National Center for Education Statistics. Yet despite near-universal adoption of access control measures, 92% of security professionals reported access control failures in the past six months, with tailgating and credential sharing identified as the most common vulnerabilities.
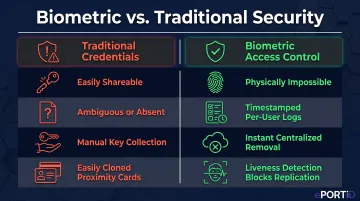
Traditional access methods—key cards, PIN codes, and physical keys—create these security failures because they authenticate what a person carries or knows, not who they actually are. Cards get lost, shared with friends, or left at home. PINs are observed and stolen. Keys are duplicated. In educational environments where thousands of people move through high-traffic entry points daily, these vulnerabilities compound rapidly.
This guide breaks down how biometric access control works in educational facilities, where it's deployed across campus zones, and what makes it fundamentally more secure than legacy credential systems.
TL;DR
- Biometric access control verifies identity using unique physical traits like palm vein patterns or facial geometry, eliminating vulnerabilities of cards or codes
- Every access event flows through three steps: enrollment captures an encrypted biometric template, live scans verify identity in under 2 seconds, and the system logs a timestamped audit trail automatically
- Schools deploy biometric readers at building perimeters, main entrances, sensitive interior areas (labs, server rooms), and residential facilities
- Unlike cards or PINs, biometric credentials cannot be shared, stolen, duplicated, or forgotten
- Implementation requires privacy compliance planning, infrastructure integration, and enrollment management across large student and staff populations
What Is Biometric Access Control for Educational Facilities?
Biometric access control is a security system that uses measurable, unique biological traits—fingerprints, iris patterns, facial geometry, or palm vein patterns—to authenticate a person's identity before granting or denying physical access to a space. Unlike traditional credentials that verify what you have (a key card) or what you know (a PIN code), biometric systems verify who you are through biological characteristics that cannot be transferred to another person.
This distinction targets the fundamental weakness in traditional school security: credential transferability. Key cards authenticate the card itself, not the person holding it. A student can lend their ID to a friend, an expelled individual can steal a staff badge, or a contractor can enter with a copied proximity card.
61% of access control failures stem from exactly these scenarios, according to ASIS International — making tailgating and credential sharing the top-ranked vulnerability across all facility types.
Biometric systems eliminate this class of security failure entirely. When a student uses palm vein scanning to enter a school building, the system verifies the unique vein pattern beneath their skin—a biological signature derived from 5 million data points that remains consistent even among identical twins. This credential cannot be lent to a friend, cannot be forgotten at home, and cannot be cloned with a card reader.
It's also worth clarifying what biometric access control is not. The system performs a discrete identity check at a specific access point—a doorway, turnstile, or gate—and records that single verification event. It does not continuously monitor movement or track behavior throughout a facility.
Educational facilities typically deploy four types of biometric technology:
- Fingerprint scanning — Captures ridge patterns from fingertips; widely recognized but requires physical contact
- Facial recognition — Analyzes facial geometry; contactless but NIST research shows false positive rates vary by 10x to 100x across demographic groups, raising equity concerns for diverse student populations
- Iris scanning — Reads unique patterns in the colored ring of the eye; highly accurate but requires user cooperation and close proximity
- Contactless palm vein scanning — Uses near-infrared light to map vein patterns beneath the skin; achieves FAR under 0.00001% and FRR of 1% with built-in liveness detection, delivering the strongest accuracy-to-hygiene ratio for school environments
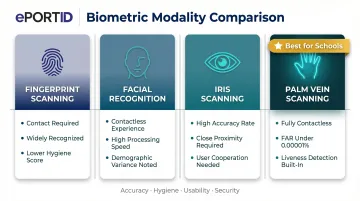
Modality selection matters because not every entry point carries the same risk. High-throughput main entrances may suit facial recognition's speed, but areas requiring the highest assurance — restricted labs, server rooms, medication storage — call for palm vein scanning's combination of accuracy, hygiene, and liveness detection.
How Does Biometric Access Control Work?
Biometric access control follows a defined multi-stage process: enrollment, verification, and access decision. Each stage builds on the last, creating a security chain that's difficult to compromise.
Enrollment: Capturing the Biometric Identity
Before the system can recognize anyone, each authorized user undergoes enrollment. A scanner captures their biometric data—for example, a contactless palm vein reader uses near-infrared light to detect the pattern of veins beneath the skin, mapping identity from millions of data points. This raw biometric data is immediately converted into a mathematical template, not a stored image.
This conversion serves two critical purposes:
- Reduces storage requirements — a mathematical representation of vein patterns occupies far less database space than high-resolution biometric images
- Strengthens privacy protection — the original biometric trait cannot be reverse-engineered from the stored template, making stolen database records worthless to attackers
The enrollment process takes approximately 15 seconds per hand for palm vein systems, making it practical to enroll large student populations during orientation or registration periods.
Verification: Matching the Live Scan
At the access point, verification happens in real time. The user presents their biometric—holding their palm over a contactless scanner or looking at a facial recognition camera—and the system captures a fresh scan, converts it to a template using the same algorithm from enrollment, then compares it against the stored profile.
Advanced biometric systems incorporate liveness detection during this verification stage. ePortID's contactless palm vein technology uses near-infrared light to verify active blood flow beneath the skin—confirming the system is reading a live biological trait rather than a photograph, silicone replica, or prosthetic. This anti-fraud mechanism achieves 99.99991% accuracy with identity derived from 5 million unique data points. Verification completes in under 2 seconds—practical for high-traffic school entrances during morning arrival.
Systems operate in two matching modes:
- 1:1 verification — The user identifies themselves (with a card tap or ID number), and the system compares the live scan to that single enrolled profile; common at restricted interior access points
- 1:N identification — The system compares the live scan against the entire enrolled database; used at main entrances where speed and convenience are prioritized
Access Decision and Audit Trail
The system generates one of two outputs: grant access (triggering an electronic door unlock, turnstile release, or gate lift) or deny access and optionally alert security personnel.
Every access event—successful or denied—is automatically logged with a timestamp, location identifier, and user ID. This real-time audit trail supports security investigations, attendance verification, and compliance reporting.
Unlike a physical key that leaves no record of use, biometric access logs document exactly who entered which area and when. That accountability is directly relevant to FERPA requirements and institutional safety policies that schools must maintain.

Where Biometric Systems Are Deployed Across Educational Campuses
Educational campuses contain multiple security zones with varying risk levels. Biometric access control is typically deployed in layers, with stricter verification requirements applied to higher-risk or more sensitive areas.
Perimeter and Main Building Entrances
Main entry points represent the first and most high-traffic deployment zone. Biometric readers at primary entrances allow fast throughput—critical during peak hours like morning drop-off or class changes—while ensuring only enrolled individuals can enter. 97% of US public schools controlled building access during school hours, yet traditional card-based systems still allow unauthorized entry through lost or shared credentials.
Contactless biometric systems designed for high-throughput environments complete verification in under 2 seconds per person. Deploying multiple readers at main entrances manages peak-hour traffic effectively while maintaining security integrity that card readers cannot match.
Sensitive Interior Areas
Not all credentialed individuals on campus should access all areas. Biometric systems enable role-based access permissions tied directly to each person's palm vein profile — a maintenance worker cannot enter a research lab, and a student cannot access a server room, because their enrollment simply doesn't authorize those zones.
Restricted areas that commonly require this additional layer include:
- Science and research laboratories
- Server rooms and data centers
- Financial offices and administrative records rooms
- IT infrastructure and utility control areas
These restricted areas often implement multi-factor authentication—combining biometric verification with RFID cards or PIN codes—so that even a stolen credential alone cannot open the door. The system generates real-time alerts when unauthorized individuals attempt entry, allowing security teams to respond before a breach occurs.
Residential Facilities and Daycare Settings
University residence halls and daycare environments present distinct security challenges. In residence halls, biometric access replaces swipe cards that students regularly lose or lend to visitors, creating unauthorized access risks. When students use their palm vein pattern for dorm entry, the administrative cycle of replacing lost cards — and the security gaps those gaps create — stops entirely.
Daycare environments raise the stakes further. Solutions like ePortID's MyKidSecure restrict facility entry to enrolled staff and authorized family members only, while automatically logging every access event. That audit trail directly addresses child custody requirements and safety regulations that paper sign-in sheets cannot reliably satisfy.
Contactless biometric modalities offer a critical advantage in these environments: they eliminate shared touchpoints. In daycares and K-12 schools where children frequently touch surfaces, contactless palm vein scanning removes the hygiene concern associated with fingerprint pads that dozens of users touch throughout the day.
Key Security Advantages Over Traditional Access Methods
Traditional credentials suffer from a fundamental flaw: they can be lost, forgotten, stolen, cloned, or deliberately shared. Despite 97% of schools controlling building access, credential vulnerabilities still account for the security failures reported by 92% of security professionals. Biometric identifiers eliminate this entire class of risk — because your identity can't be handed to someone else. Here's where that difference shows up in practice.
Biometric systems close four specific gaps that traditional credentials leave open:
- Credential sharing is physically impossible. University students lend ID cards; staff check in late colleagues. 75% of businesses are affected by buddy punching, costing US employers $373 million annually. Biometric verification ties every access event to one verified person — no proxies, no workarounds.
- Audit trails support compliance and investigations. A physical key leaves no record. A shared PIN creates ambiguous logs. Biometric systems generate timestamped entries for every attempt — successful or denied — documenting who accessed which area and when. These records satisfy FERPA tracking requirements and hold up during safety audits.
- Centralized management closes gaps instantly. When a student is expelled or a staff member is terminated, administrators revoke access across all networked entry points in seconds — no key collection, no lock changes. Thousands of users across multiple buildings update from a single platform.
- Cloning is not a viable attack vector. Legacy 125 kHz proximity cards remain widely deployed despite being easily cloned — wirelessly, with low-cost hardware, without ever touching the card. Biometric identifiers can't be photographed or replicated; liveness detection confirms the system is reading a live biological trait, not a reproduction.
What to Consider Before Implementing Biometric Access Control
Privacy and Data Governance
Schools must communicate transparently about what biometric data is collected, how it's stored, who accesses it, and how long it's retained. Modern biometric systems store mathematical templates rather than actual images, making it impossible to reconstruct the original biometric trait from stored data.
Some jurisdictions impose specific legal requirements. Illinois' Biometric Information Privacy Act (BIPA) requires written consent before collecting biometric information, mandates written retention and destruction policies, and creates private right of action with damages of $1,000 per negligent violation or $5,000 per intentional violation. Similar laws exist in Texas, Colorado, Washington, and New York City. Schools in these jurisdictions must implement consent workflows, retention schedules, and data governance policies before deploying biometric systems.
Integration and Infrastructure
Many educational institutions already operate legacy access control systems, network infrastructure, and identity management platforms. Biometric systems must integrate with existing hardware—door controllers, access panels, electric strikes—and software platforms without requiring complete infrastructure replacement.
Modern biometric platforms connect via standard protocols including OSDP (Open Supervised Device Protocol) and Wiegand interfaces. OSDP provides AES-128 encryption and bi-directional communication versus Wiegand's unencrypted, one-way design, making OSDP the preferred standard for new installations.
Power over Ethernet (PoE) deployment enables biometric readers to operate up to 100 meters from the power source using standard network cabling, minimizing installation complexity.
Integration extends beyond physical hardware. Biometric systems should connect with:
- Student information systems for automated roster updates
- Attendance platforms to log entry and exit in real time
- Visitor management software for unified campus reporting
- HR and identity management platforms to sync staff credentials

Enrollment and Adoption
For biometric systems to work, every authorized user must be enrolled. This means managing enrollment for large, rotating populations: new students each semester, seasonal staff, authorized parents in daycare settings, and visiting researchers on university campuses.
Contactless systems with fast verification times reduce enrollment friction and increase adoption rates. When enrollment takes 15 seconds per person and verification completes in under 2 seconds, the system feels effortless rather than burdensome—a real advantage in high-turnover environments where a clunky process leads staff and students to route around the system entirely.
That enrollment experience also shapes rollout strategy. Institutions planning renovations or security upgrades can phase in biometric systems incrementally—starting with highest-risk areas like server rooms and laboratories before expanding to main entrances and residential facilities.
Frequently Asked Questions
What types of biometric technology are most commonly used in schools and universities?
Schools use several biometric modalities, including facial recognition, fingerprint scanners, and contactless palm vein scanners. For educational settings, palm vein scanning offers the strongest combination: it's contactless, accurate across diverse populations, and checks for liveness during every scan — a critical advantage where student health and equity both matter.
Is biometric data stored securely, and can it be hacked or stolen?
Modern systems store encrypted mathematical templates — not biometric images — making it impossible to reconstruct the original trait from stored data. These templates are encrypted in transit and at rest, and biometric networks are typically isolated from main campus networks with dedicated firewall protection.
Can students or staff refuse to use a biometric system?
Yes. Some jurisdictions require written consent before enrollment, and institutions typically offer alternative access methods — RFID cards or PIN codes — for those who opt out. This is worth planning for, as opt-outs reduce the system's security consistency across all entry points.
How do biometric systems handle large numbers of people entering a school at the same time?
Modern contactless systems complete verification in under 2 seconds per person, and deploying multiple readers at entry points manages peak-hour traffic effectively. High-throughput modalities like palm vein and facial recognition are designed for morning arrival periods when hundreds of students enter designed for morning arrival periods when hundreds of students enter simultaneously.
How does biometric access control differ from a standard key card or PIN system?
Key cards and PINs verify what a person has or knows—both of which can be transferred, shared, lost, or stolen. Biometrics verify who the person actually is through unique biological traits, making credential sharing, cloning, or theft operationally impossible.
Can biometric access control be integrated with existing school security infrastructure?
Yes. Modern biometric platforms use standard APIs and protocols (OSDP, Wiegand) to connect with existing access control software, video surveillance, time-and-attendance, and visitor management systems. Education-focused solutions like ePortID's MySchoolSecure and MyCampusSecure are built specifically for K-12 and university environments, minimizing the need for full infrastructure replacement.